3.3 Expansion
Once an adversary gains access to the target’s technology resources, typically they engage in a recursive process in which they establish persistence, conduct reconnaissance, update their attack strategy, and broaden their access. These activities build off each other and often occur at the same time, rather than in a clear linear progression, as illustrated in Figure 3.2.
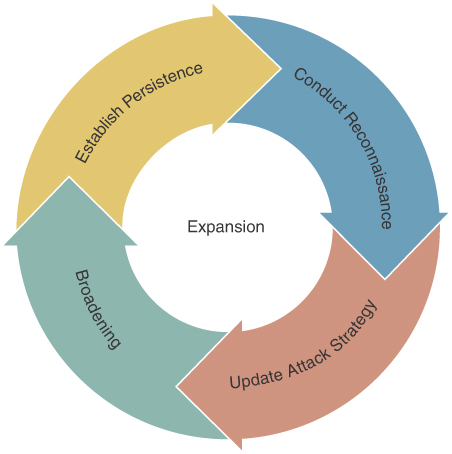
Figure 3.2 The “expansion” phase of a cyber extortion attack
Activities at this stage include the following steps:
Establish persistence: The adversary works to establish sustained, reliable access over an extended period of time and evade detection. To accomplish this, the adversary may install remote access tools, neutralize antivirus software, add new accounts, and so on.
Conduct reconnaissance: The adversary gathers information that will enable them to expand the scope of compromise. This may include network mapping, password cracking and interception, and more.
Update the attack strategy: The adversary uses the information gleaned to refine their goals, plan, and processes.
Broadening: The adversary increases their access to systems, accounts, or other network resources, by escalating privileges, moving laterally through the network, and gaining access to different applications and technology resources.
Along the way, all of the adversary’s activities provide defenders with opportunities to detect and eradicate the threat. Each interaction generates unique and identifiable indicators that a security team can monitor to identify the threat.
In particular, during the early stages of an attack, the adversary is at their most vulnerable, since they are likely still unfamiliar with the network topography and may unwittingly create “noise” while engaging in network reconnaissance and other expansion activities. The method of access and the adversary’s skill set can also vary significantly, leading to variations in IoCs and detection strategy.
In the following sections, we describe specific indicators of compromise that can facilitate detection and enable defenders to break the chain of attack.
3.3.1 Persistence
Simply gaining access to a victim’s network once is not usually sufficient to gain extensive leverage over a victim. Instead, the adversary must find a way to access resources on the victim’s network repeatedly over a sustained period of time.
Frequently, the adversary lurks on the network for an extended period of time (even weeks or months) prior to gaining leverage (e.g., exfiltrating data, detonating ransomware). This means that the target has an opportunity to detect and eradicate the compromise before the worst occurs.
Opportunities for Detection
The specific indicators of compromise vary based on the method of access, but almost universally, the adversary needs to generate periodic network traffic. They often use a command-and-control server, otherwise known as a C2 server, in which an infected endpoint “phones home” to an adversary-controlled server. They may also use standard IT remote access tools such as RDP, Anydesk, or others.
Defenders should be on the lookout for telltale signs of suspicious network activity:
Suspicious source/destination IP addresses and domains
Network communication originating from unfamiliar or unexpected processes
Malformed communications—for example, DNS requests with Base64 encoded content instead of normal URLs
Unauthorized remote access attempts
3.3.2 Reconnaissance
Now that the adversary has established a consistent method of entering the environment, they will often perform information gathering tasks to better understand the network, its connected devices, and potential targets for further exploitation. The adversary can perform these activities using built-in system tools, third-party software, or both. The adversary will often look for the following items:
Local IP address range information
Available subnets
Domain information
Available network services
DNS information
Using information gathered from the network, the adversary can effectively map the environment they now have access to and determine their best options for additional actions after the initial compromise. Additionally, because system administrators often include function descriptions in network computer names (i.e., Fileserver-01 or DC-01), the adversary can specifically target anything that they identify as a potentially high-impact target.
Often, indicators of network reconnaissance are observed during the early stages of an incident. This provides an opportunity to greatly reduce an adversary’s ability to spread through the network or possibly stop it entirely.
Opportunities for Detection
The following indicators can signal potentially malicious network reconnaissance:
Indicators of port scanning (NMAP)
Increased network resource usage from suspicious computers
Outbound network traffic spikes at irregular hours
Increased outbound network traffic
3.3.3 Broadening
Once the initial foothold is secured, the adversary works to expand access to additional network resources, including high-value systems that hold confidential information or can be used to control resources. Along the way, the adversary will attempt to gain additional privileges, specifically targeting domain administrator privileges and administrative access to cloud tenants/applications. Typically, the adversary’s activities include at least the following:
Privilege escalation: The adversary attempts to gain a higher level of user privileges. In the early stages, this is often accomplished by scraping credentials from system memory using a tool such as Mimikatz, extracting saved passwords from web browsers, capturing Kerberos tokens, or simply searching the infected host for documented credentials. Once the adversary has moved laterally throughout the network, they may engage in more sophisticated privilege escalation attacks involving theft of private keys, Security Assertion Markup Language (SAML) token forgery, and more.
Lateral movement: The adversary attempts to gain access to other hosts on the network by using stolen passwords, exploiting vulnerabilities, or applying other tactics. Commonly, this process is facilitated by the widespread practice of configuring a static local administrator password shared by all endpoints.
Application/cloud access: The adversary accesses applications and cloud tenants, typically by using stolen passwords or leveraging trust relationships between local systems and services.
If an adversary is able to establish a significant breadth of access, it becomes much more difficult to fully eradicate the threat.
Opportunities for Detection
Common indicators of broadening or expanding access by adversaries include the following:
Unusual Local Administrator account activities, including network authentications or shared folder access
Connections to core assets from unusual or unauthorized workstations
Suspicious application access
Impossible travel alerts
