- 1.1 Opinions, Products
- 1.2 Roadmap to the Book
- 1.3 Terminology
- 1.4 Notation
- 1.5 Cryptographically Protected Sessions
- 1.6 Active and Passive Attacks
- 1.7 Legal Issues
- 1.8 Some Network Basics
- 1.9 Names for Humans
- 1.10 Authentication and Authorization
- 1.11 Malware: Viruses, Worms, Trojan Horses
- 1.12 Security Gateway
- 1.13 Denial-of-Service (DoS) Attacks
- 1.14 NAT (Network Address Translation)
1.11 Malware: Viruses, Worms, Trojan Horses
Lions and tigers and bears, oh my!
—Dorothy (in the movie The Wizard of Oz)
People like to categorize different types of malicious software and assign them cute biological terms (if one is inclined to think of worms as cute). We don’t think it’s terribly important to distinguish between these things, so in the book we’ll refer to all kinds of malicious software generically as malware. However, here are some of the terms that seem to be infecting the literature.
Trojan horse—instructions hidden inside an otherwise useful program that do bad things. Usually, the term Trojan horse is used when the malicious instructions are installed at the time the program is written (and the term virus is used if the instructions get added to the program later).
virus—a set of instructions that, when executed, inserts copies of itself into other programs.
worm—a program that replicates itself by installing copies of itself on other machines across a network.
trapdoor—an undocumented entry point intentionally written into a program, often for debugging purposes, which can be exploited as a security flaw. Often people forget to take these out when the product ships. However, sometimes these undocumented “features” are intentionally put into software by an employee who thinks he might at some point become disgruntled.
bot—a machine that has been infected with malicious code that can be activated to do some malicious task by some controller machine across the Internet. The controller is often referred to as a bot herder. The intention of the disease-infected rodents (apologies if we offend actual disease-infected rodents who might be reading this book) who turn a computer into a bot is that the owner of the machine should not be aware that their machine is infected. To the owner of the machine, it continues operating as usual. However, the controller can at some point rally all the bots under its control to do some sort of mischief like sending out spam or flooding some service with nuisance messages. The bots under its control are often referred to as a bot army. There are price lists on the dark web for renting a bot army, priced according to the size of the army and the amount of time you would like to rent them. (The dark web is a subset of the Internet that is not visible to search engines, and requires special access mechanisms. It is an ideal place for purchasing illegal goods.)
logic bomb—malicious instructions that trigger on some event in the future, such as a particular time occurring. The delay might advantage criminals that create a logic bomb, because they can first deploy the logic bomb in many places. Or, they can make the bad event occur long after they have left the company, so they won’t be under suspicion.
ransomware—malicious code that encrypts the user’s data, and then the helpful criminal offers to help get the data back, for a small fee (such as several million dollars).
Most of the items above exploit bugs in operating systems or applications. There are also vulnerabilities that exploit bugs in humans. One example is phishing, the act of sending email to a huge unstructured list of email addresses, that will trick some small percentage of the recipients into infecting their own machines, or divulging information such as a credit card number. Spear phishing means sending custom messages to a more focused group of people.
1.11.1 Where Does Malware Come From?
Where do these nasties come from? Originally, it was hobbyists just experimenting with what they could do. Today, big money can be made with malware. A bot army can be rented to someone that wants to damage a competitor, or a political organization they disagree with. And malware can be used for demanding ransoms. It is also used by sophisticated spy organizations. A notable example is Stuxnet. This was malware aimed specifically at damaging a certain type of equipment (centrifuges) used in Iran, to slow Iran’s ability to produce nuclear weapons.
How could an implementer get away with intentionally writing malware into a program? Wouldn’t someone notice by looking at the program? A good example of how hard it can be to decipher what a program is doing, even given the source code, is the following nice short program, written by Ian Phillipps (see Figure 1-2).
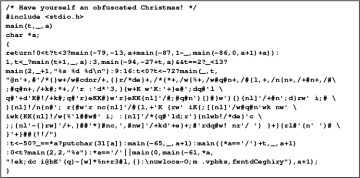
Figure 1-2. Christmas Card?
It was a winner of the 1988 International Obfuscated C Code Contest. It is delightful as a Christmas card. It does nothing other than its intended purpose (I1 have analyzed the thing carefully and I2 have complete faith in me1), but we doubt many people would take the time to understand this program before running it
But also, nobody looks. Often when you buy a program, you do not have access to the source code, and even if you did, you probably wouldn’t bother reading it all, or reading it very carefully. Many programs that run have never been reviewed by anybody. A claimed advantage of the “open source” movement (where all software is made available in source code format) is that even if you don’t review it carefully, there is a better chance that someone else will.
What does a virus look like? A virus can be installed in just about any program by doing the following:
replace any instruction, say the instruction at location x, by a jump to some free place in memory, say location y; then
write the virus program starting at location y; then
place the instruction that was originally at location x at the end of the virus program, followed by a jump to x+1.
Besides doing whatever damage the virus program does, it might replicate itself by looking for any executable files in any directory and infecting them. Once an infected program is run, the virus is executed again, to do more damage and to replicate itself to more programs. Most viruses spread silently until some triggering event causes them to wake up and do their dastardly deeds. If they did their dastardly deeds all the time, they wouldn’t spread as far.
1.11.2 Virus Checkers
How can a program check for viruses? There’s rather a race between the brave and gallant people who analyze the viruses and write clever programs to detect and eliminate them, and the foul-smelling scum who devise new types of viruses that will escape detection by all the current virus checkers.
The oldest form of virus checker knows instruction sequences that have appeared in known viruses, but are believed not to occur in benign code. It checks all the files on disk and instructions in memory for those patterns of commands, and raises a warning if it finds a match hidden somewhere inside some file. Once you own such a virus checker, you need to periodically get updates of the patterns file that include the newest viruses.
To evade detection of their viruses, virus creators have devised what are known as a polymorphic viruses. When they copy themselves, they change the order of their instructions or change instructions to functionally similar instructions. A polymorphic virus may still be detectable, but it takes more work, and not just a new pattern file. Modern virus checkers don’t just periodically scan the disk. They actually hook into the operating system and inspect files before they are written to disk.
Another type of virus checker takes a snapshot of disk storage by recording the information in the directories, such as file lengths. It might even take message digests of the files. It is designed to run, store the information, and then run again at a future time. It will warn you if there are suspicious changes. One virus, wary of changing the length of a file by adding itself to the program, compressed the program so that the infected program would wind up being the same length as the original. When the program was executed, the uncompressed portion containing the virus decompressed the rest of the program, so (other than the virus portion) the program could run normally.
Some viruses attack the virus checkers rather than just trying to elude them. If an attacker can penetrate a company that disseminates code, such as virus signatures or program patches, they can spread their malware to all the customers of that company.
