Problems
17.1. Let X be an integer variable represented with 64 bits. The probability is  that X is in the range (0, 216 − 1), the probability is
that X is in the range (0, 216 − 1), the probability is  that X is in the range (216, 232 − 1), and the probability
that X is in the range (216, 232 − 1), and the probability  is that X is in the range (232, 264 − 1). Within each range the values are equally likely. Compute the entropy of X.
is that X is in the range (232, 264 − 1). Within each range the values are equally likely. Compute the entropy of X.
17.2. A set of equally likely weather messages are: sunny (S), cloudy (C), light rain (L), and heavy rain (H). Given the added information concerning the time of day (morning or afternoon), the probabilities change as follows:
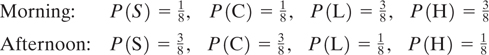
a. Find the entropy of the weather message.
b. Find the entropy of the message conditioned on the time of day.
17.3. The Hawaiian alphabet has only 12 letters—the vowels, a, e, i, o, u, and the consonants, h, k, l, m, n, p, w. Assume that each vowel occurs with probability 0.116 and that each consonant occurs with probability 0.06. Also assume that the average number of information bits per letter is the same as that for the English language. Calculate the unicity distance for an encrypted Hawaiian message if the key sequence consists of a random permutation of the 12-letter alphabet.
17.4. Estimate the unicity distance for an English language encryption system that uses a key sequence made up of 10 random alphabetic characters:
a. Where each key character can be any one of the 26 letters of the alphabet (duplicates are allowed).
b. Where the key characters may not have any duplicates.
17.5. Repeat Problem 17.4 for the case where the key sequence is made up of ten integers randomly chosen from the set of numbers 0 to 999.
17.6.
a. Find the unicity distance for a DES system which encrypts 64-bit blocks (eight alphabetic characters) using a 56-bit key.
b. What is the effect on the unicity distance in part (a) if the key is increased to 128 bits?
17.7. In Figures 17.8 and 17.9, P-boxes and S-boxes alternate. Is this arrangement any more secure than if all the P-boxes were first grouped together, followed by all the S-boxes similarly grouped together? Justify your answer.
17.8. What is the output of the first iteration of the DES algorithm when the plaintext and the key are each made up of zero sequences?
17.9. Consider the 10-bit plaintext sequence 0 1 0 1 1 0 1 0 0 1 and its corresponding ciphertext sequence 0 1 1 1 0 1 1 0 1 0, where the rightmost bit is the earliest bit. Describe the five-stage linear feedback shift register (LFSR) that produced the key sequence and show the initial state of the register. Is the output sequence of maximal length?
17.10. Following the RSA algorithm and parameters in Example 17.5, compute the encryption key, e, when the decryption key is chosen to be 151.
17.11. Given e and d that satisfy ed modulo- ϕ(n) = 1, and a message that is encoded as an integer number, M, in the range (0, n - 1) such that the gcd (M, n) = 1. Prove that (Me modulo-n)d modulo-n = M.
17.12. Use the RSA scheme to encrypt the message M = 3. Use the prime numbers p = 5 and q = 7. Choose the decryption key, d, to be 11, and calculate the value of the encryption key, e.
17.13. Consider the following for the RSA scheme.
a. If the prime numbers are p = 7 and q = 11, list five allowable values for the decryption key, d.
b. If the prime numbers are p = 13, q = 31, and the decryption key is d = 37, find the encryption key, e, and describe how you would use it to encrypt the word “DIGITAL.”
17.14. Use the Merkle–Hellman public key scheme with the super-increasing vector, a = 1, 3, 5, 10, 20. Use the following additional parameters: a large prime number M = 51 and a random number W = 37.
a. Find the nonsuper-increasing vector, a, to be made public, and encrypt the data vector 1 1 0 1 1.
b. Show the steps by which an authorized receiver decrypts the ciphertext.
17.15. Using the Diffie-Hellman (Elgamal variation) protocol, encrypt the message M = 7. The system parameters are n = 17 and g = 3. The recipient s private key is a = 4. Determine the recipient’s public key. For message encryption with the randomly selected k, use k = 2. Verify the accuracy of the ciphertext by performing decryption using the recipient’s private key.
17.16. Find the hexadecimal (hex) value of the message “no” after one round of the IDEA algorithm. The session key in hex notation is = 0002 0003 0002 0003 0002 0003 0002 0003, where the rightmost 4-digit group represents the subkey Z1. For the message “no,” let each ASCII character be represented by a 16-bit data subblock, where “n” = 006E and “o” = 006F.
17.17. In the PGP Example 17.10, the IDEA session key is encrypted using the RSA algorithm. The resulting encrypted session key (in base-10 notation) was: 0000 2227 0000 2704 0753 0001 1278 0272 0001 1405 0272 0001, where the least significant (rightmost) group is group 1. Using the decryption key, decrypt group 11 of this session key using the Square-and-Multiply technique.
