Encryption and Decryption in Digital Communications
- 17.1 Models, Goals, and Early Cipher Systems
- 17.2 The Secrecy of a Cipher System
- 17.3 Practical Security
- 17.4 Stream Encryption
- 17.5 Public Key Cryptosystems
- 17.6 Pretty Good Privacy
- 17.7 Conclusion
- References
- Problems
- Questions
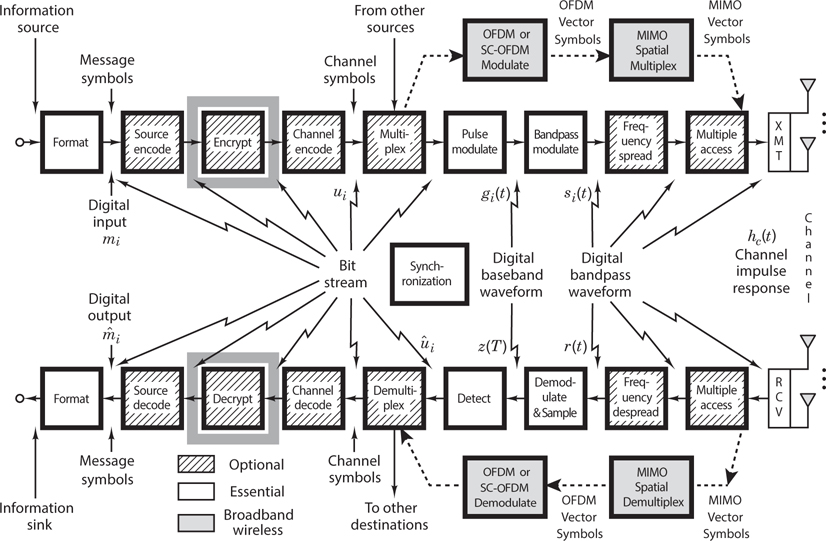
17.1 Models, Goals, and Early Cipher Systems
17.1.1 A Model of the Encryption and Decryption Process
The desire to communicate privately is a human trait that dates back to earliest times. Hence the history of secret communications is rich with unique inventions and colorful anecdotes [1]. The study of ways to disguise messages so as to avert unauthorized interception is called cryptography. The terms encipher and encrypt refer to the message transformation performed at the transmitter, and the terms decipher and decrypt refer to the inverse transformation performed at the receiver. The two primary reasons for using cryptosystems in communications are (1) privacy, to prevent unauthorized persons from extracting information from the channel (eavesdropping); and (2) authentication, to prevent unauthorized persons from injecting information into the channel (spoofing). Sometimes, as in the case of electronic funds transfer or contract negotiations, it is important to provide the electronic equivalent of a written signature in order to avoid or settle any dispute between the sender and receiver as to what message, if any, was sent.
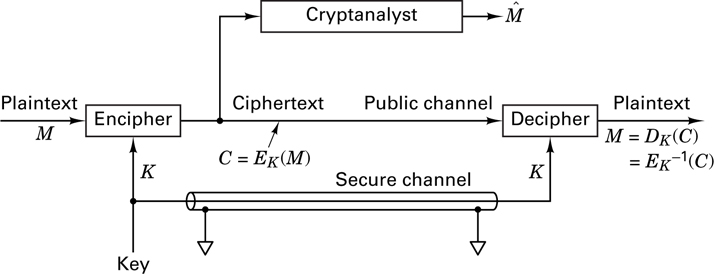
Figure 17.1 illustrates a model of a cryptographic channel. A message, or plaintext, M, is encrypted by the use of an invertible transformation, EK, that produces a ciphertext, C = EK(M). The ciphertext is transmitted over an insecure or public channel. When an authorized receiver obtains C, he decrypts it with the inverse transformation,  , to obtain the original plaintext message, as follows:
, to obtain the original plaintext message, as follows:

The parameter K refers to a set of symbols or characters called a key, which dictates a specific encryption transformation, EK, from a family of cryptographic transformations. Originally, the security of cryptosystems depended on the secrecy of the entire encryption process, but eventually systems were developed for which the general nature of the encryption transformation or algorithm could be publicly revealed, since the security of the system depended on the specific key. The key is supplied along with the plaintext message for encryption, and along with the ciphertext message for decryption. There is a close analogy here with a general-purpose computer and a computer program. The computer, like the cryptosystem, is capable of a large variety of transformations, from which the computer program, like the specific key, selects one. In most cryptosystems, anyone with access to the key can both encrypt and decrypt messages. The key is transmitted to the community of authorized users over a secure channel (as an example, a courier may be used to hand-carry the sensitive key information); the key usually remains unchanged for a considerable number of transmissions. The goal of the cryptanalyst (eavesdropper or adversary) is to produce an estimate of the plaintext,  , by analyzing the ciphertext obtained from the public channel, without benefit of the key.
, by analyzing the ciphertext obtained from the public channel, without benefit of the key.
Encryption schemes fall into two generic categories: block encryption, and data-stream or simply stream encryption. With block encryption, the plaintext is segmented into blocks of fixed size; each block is encrypted independently from the others. For a given key, a particular plaintext block will therefore be carried into the same ciphertext block each time it appears (similar to block encoding). With data-stream encryption, similar to convolutional coding, there is no fixed block size. Each plaintext bit, mi, is encrypted with the ith element, ki, of a sequence of symbols (key stream) generated with the key. The encryption is periodic if the key stream repeats itself after p characters for some fixed p; otherwise, it is nonperiodic.
In general, the properties desired in an encryption scheme are quite different from those desired in a channel coding scheme. For example, with encryption, plaintext data should never appear directly in the ciphertext, but with channel coding, codes are often in systematic form comprising unaltered message bits plus parity bits (see Section 6.4.5). Consider another example of the differences between encryption and channel coding. With block encryption, a single bit error at the input of the decryptor might change the value of many of the output bits in the block. This effect, known as error propagation, is often a desirable cryptographic property since it makes it difficult for unauthorized users to succeed in spoofing a system. However, in the case of channel coding, we would like the system to correct as many errors as possible, so that the output is relatively unaffected by input errors.
17.1.2 System Goals
The major requirements for a cryptosystem can be stated as follows:
To provide an easy and inexpensive means of encryption and decryption to all authorized users in possession of the appropriate key
To ensure that the cryptanalyst’s task of producing an estimate of the plain-text without benefit of the key is made difficult and expensive
Successful cryptosystems are classified as being either unconditionally secure or computationally secure. A system is said to be unconditionally secure when the amount of information available to the cryptanalyst is insufficient to determine the encryption and decryption transformations, no matter how much computing power the cryptanalyst has available. One such system, called a one-time pad, involves encrypting a message with a random key that is used one time only. The key is never reused; hence the cryptanalyst is denied information that might be useful against subsequent transmissions with the same key. Although such a system is unconditionally secure (see Section 17.2.1), it has limited use in a conventional communication system, since a new key would have to be distributed for each new message—a great logistical burden. The distribution of keys to the authorized users is a major problem in the operation of any cryptosystem, even when a key is used for an extended period of time. Although some systems can be proven to be unconditionally secure, currently there is no known way to demonstrate security for an arbitrary cryptosystem. Hence the specifications for most cryptosystems rely on the less formal designation of computational security for x number of years, which means that under circumstances favorable to the cryptanalyst (i.e., using state-of-the-art computers) the system security could be broken in a period of x years, but could not be broken in less than x years.
17.1.3 Classic Threats
The weakest classification of cryptanalytic threat on a system is called a ciphertext-only attack. In this attack the cryptanalyst might have some knowledge of the general system and the language used in the message, but the only significant data available to him is the encrypted transmission intercepted from the public channel.
A more serious threat to a system is called a known plaintext attack; it involves knowledge of the plaintext and knowledge of its ciphertext counterpart. The rigid structure of most business forms and programming languages often provides an opponent with much a priori knowledge of the details of the plaintext message. Armed with such knowledge and with a ciphertext message, the cryptanalyst can mount a known plaintext attack. In the diplomatic arena, if an encrypted message directs a foreign minister to make a particular public statement, and if he does so without paraphrasing the message, the cryptanalyst may be privy to both the ciphertext and its exact plaintext translation. While a known plaintext attack is not always possible, its occurrence is frequent enough that a system is not considered secure unless it is designed to be secure against the plaintext attack [2].
When the cryptanalyst is in the position of selecting the plaintext, the threat is termed a chosen plaintext attack. Such an attack was used by the United States to learn more about the Japanese cryptosystem during World War II. On May 20, 1942, Admiral Yamamoto, Commander-in-Chief of the Imperial Japanese Navy, issued an order spelling out the detailed tactics to be used in the assault of Midway island. This order was intercepted by the Allied listening posts. By this time, the Americans had learned enough of the Japanese code to decrypt most of the message. Still in doubt, however, were some important parts, such as the place of the assault. They suspected that the characters “AF” meant Midway island, but to be sure, Joseph Rochefort, head of the Combat Intelligence Unit, decided to use a chosen plaintext attack to trick the Japanese into providing concrete proof. He had the Midway garrison broadcast a distinctive plaintext message in which Midway reported that its fresh-water distillation plant had broken down. The American cryptanalysts needed to wait only two days before they intercepted a Japanese ciphertext message stating that AF was short of fresh water [1].
17.1.4 Classic Ciphers
One of the earliest examples of a monoalphabetic cipher was the Caesar Cipher, used by Julius Caesar during the Gallic wars. Each plaintext letter is replaced with a new letter obtained by an alphabetic shift. Figure 17.2a illustrates such an encryption transformation, consisting of three end-around shifts of the alphabet. When using this Caesar’s alphabet, the message, “now is the time” is encrypted as follows:
Plaintext: |
N |
O |
W |
I |
S |
T |
H |
E |
T |
I |
M |
E |
Ciphertext: |
Q |
R |
Z |
L |
V |
W |
K |
H |
W |
L |
P |
H |
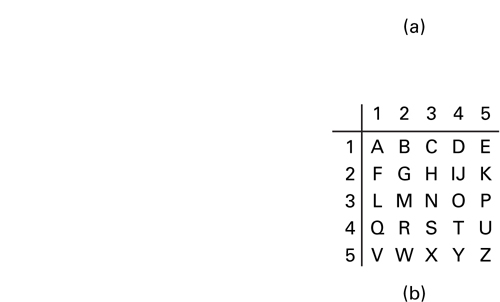
The decryption key is simply the number of alphabetic shifts; the code is changed by choosing a new key. Another classic cipher system, illustrated in Figure 17.2b, is called the Polybius square. Letters I and J are first combined and treated as a single character since the final choice can easily be decided from the context of the message. The resulting 25 character alphabet is arranged in a 5 × 5 array. Encryption of any character is accomplished by choosing the appropriate row-column (or column-row) number pair. An example of encryption with the use of the Polybius square follows:
Plaintext: |
A |
B |
C |
D |
E |
F |
G |
H |
I |
J |
K |
L |
M |
N |
O |
P |
Q |
R |
S |
T |
U |
V |
W |
X |
Y |
Z |
Chiphertext: |
D |
E |
F |
G |
H |
I |
J |
K |
L |
M |
N |
O |
P |
Q |
R |
S |
T |
U |
V |
W |
X |
Y |
Z |
A |
B |
C |
Plaintext: |
N |
O |
W |
I |
S |
T |
H |
E |
T |
I |
M |
E |
Ciphertext: |
33 |
43 |
25 |
42 |
34 |
44 |
32 |
51 |
44 |
42 |
23 |
51 |
The code is changed by a rearrangement of the letters in the 5 × 5 array.
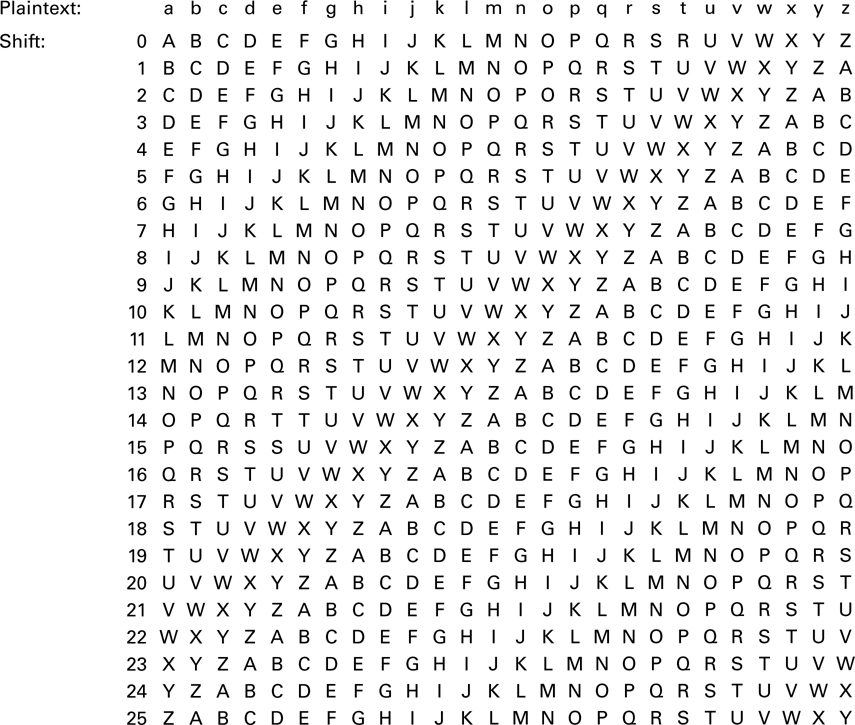
The Trithemius progressive key, shown in Figure 17.3, is an example of a polyalphabetic cipher. The row labeled shift 0 is identical to the usual arrangement of the alphabet. The letters in the next row are shifted one character to the left with an end-around shift for the leftmost position. Each successive row follows the same pattern of shifting the alphabet one character to the left as compared to the prior row. This continues until the alphabet has been depicted in all possible arrangements of end-around shifts. One method of using such an alphabet is to select the first cipher character from the shift 1 row, the second cipher character from the shift 2 row, and so on. An example of such encryption is
Plaintext: |
N |
O |
W |
I |
S |
T |
H |
E |
T |
I |
M |
E |
Ciphertext: |
O |
Q |
Z |
M |
X |
Z |
O |
M |
C |
S |
X |
Q |
There are several interesting ways that the Trithemius progressive key can be used. One way, called the Vigenere key method, employs a keyword. The key dictates the row choices for encryption and decryption of each successive character in the message. For example, suppose that the word “TYPE” is selected as the key; then an example of the Vigenere encryption method is
Key: |
T |
Y |
P |
E |
T |
Y |
P |
E |
T |
Y |
P |
E |
Plaintext: |
N |
O |
W |
I |
S |
T |
H |
E |
T |
I |
M |
E |
Ciphertext: |
G |
M |
L |
M |
L |
R |
W |
I |
M |
G |
B |
I |
where the first letter, T, of the key indicates that the row choice for encrypting the first plaintext character is the row starting with T (shift 19). The next row choice starts with Y (shift 24), and so on. A variation of this key method, called the Vigenere auto (plain) key method, starts with a single letter or word used as a priming key. The priming key dictates the starting row or rows for encrypting the first or first few plaintext characters, as in the preceding example. Next, the plaintext characters themselves are used as the key for choosing the rows for encryption. An example using the letter “F” as the priming key is
Key: |
F |
N |
O |
W |
I |
S |
T |
H |
E |
T |
I |
M |
Plaintext: |
N |
O |
W |
I |
S |
T |
H |
E |
T |
I |
M |
E |
Ciphertext: |
S |
B |
K |
E |
A |
L |
A |
L |
X |
B |
U |
Q |
With the auto key method, it should be clear that feedback has been introduced to the encryption process. With this feedback, the choice of the ciphertext is dictated by the contents of the message.
A final variation of the Vigenere method, called the Vigenere auto (cipher) key method, is similar to the plain key method in that a priming key and feedback are used. The difference is that after encryption with the priming key, each successive key character in the sequence is obtained from the prior ciphertext character instead of from the plaintext character. An example should make this clear; as before, the letter “F” is used as the priming key:
Key: |
F |
S |
G |
C |
K |
C |
V |
C |
G |
Z |
H |
T |
Plaintext: |
N |
O |
W |
I |
S |
T |
H |
E |
T |
I |
M |
E |
Ciphertext: |
S |
G |
C |
K |
C |
V |
C |
G |
Z |
H |
T |
X |
Although each key character can be found from its preceding ciphertext character, it is functionally dependent on all the preceding characters in the message plus the priming key. This has the effect of diffusing the statistical properties of the plaintext across the ciphertext, making statistical analysis very difficult for a cryptanalyst. One weakness of the cipher key example depicted here is that the ciphertext contains key characters which will be exposed on the public channel “for all to see.” Variations of this method can be employed to prevent such overt exposure[3]. By today’s standards Vigenere’s encryption schemes are not very secure; his basic contribution was the discovery that nonrepeating key sequences could be generated by using the messages themselves or functions of the messages.