- Why Agile Product Delivery?
- Customer Centricity and Design Thinking
- Develop on Cadence, Release on Demand
- DevOps and the Continuous Delivery Pipeline
- Summary
DevOps and the Continuous Delivery Pipeline
The third dimension of Agile product delivery is DevOps and the CDP. The capability to release reliably and with high quality, whenever the market or customer demands, requires embracing the DevOps mindset and culture and creating an automated CDP.
Embracing DevOps Mindset, Culture, and Practices
As digital disruption continues to change the world and as software plays a more significant role in every company’s ability to deliver and support its products and services, enterprises need to react faster to customer demands with digital solutions.
Popularized by The Phoenix Project10 and The DevOps Handbook,11 the DevOps movement seeks to better align development, operations, the business, information security, and other areas by sharing the work and responsibility for accelerating delivery.
DevOps is the adoption of a mindset, culture, and set of practices that provide solution elements to the customer without handoffs and without requiring excessive production or operations support.
SAFe’s CALMR approach (Figure 7-19) to DevOps is grounded in five concepts: Culture, Automation, Lean flow, Measurement, and Recovery.

Figure 7-19. A CALMR approach to DevOps
Culture represents the philosophy of shared responsibility for fast value delivery across the entire value stream.
Automation represents the need to remove as much human intervention from the pipeline as possible to decrease errors and reduce the cycle time of the release process.
Lean flow identifies the practices of limiting WIP, reducing batch size, and managing queue lengths (SAFe Principle #6).
Measurement fosters learning and continuous improvement by understanding and quantifying the flow of value through the pipeline.
Recovery builds systems that allow fast fixes of production issues through automatic rollback and fix-forward (in production) capabilities.
DevSecOps
DevOps, however, isn’t merely about development and operations. In the past, a specific group was dedicated to security testing toward the end of implementation. This practice was less of an issue when phase-gated development cycles lasted months or years. Today, outdated security practices can undo even the most efficient DevOps initiatives and have unacceptably high social and financial costs. It has become so critical that many use the phrase ‘DevSecOps’ to emphasize how essential it is to integrate security into the CDP.
The Continuous Delivery Pipeline
The CDP represents the workflows, activities, and automation needed to guide a new piece of functionality from ideation to an on-demand release of value to the end-user. As illustrated in Figure 7-20, the pipeline consists of four aspects: Continuous Exploration (CE), Continuous Integration (CI), Continuous Deployment (CD), and Release on Demand (RoD).
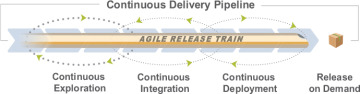
Figure 7-20. The SAFe continuous delivery pipeline
Each ART builds and maintains, or shares with other ARTs, a pipeline with the assets and technologies needed to deliver solution value as independently as possible. The first three elements of the pipeline (CE, CI, and CD) work together to support the delivery of small batches of new functionality, which are then released to meet market demand.
Continuous Exploration
CE fosters continuing research and alignment on what should be built. Design thinking continually explores market and customer needs and defines a vision, roadmap, and a set of features that meets those needs. During this period, new ideas are raised, refined, and prepared as a list of prioritized features in the program backlog. During CE planning, features are pulled into implementation, which begins the continuous integration process.
There are four main CE activities described in SAFe (Figure 7-21):
Hypothesize describes the practices necessary to identify ideas and the measurements needed to validate them with customers.
Collaborate and research describes the practices required to work with customers and stakeholders to refine the understanding of potential needs.
Architect describes the practices necessary to envision a technical approach that enables quick implementation, delivery, and support of ongoing operations.
Synthesize describes the practices that organize the ideas into a holistic vision, a roadmap, and a prioritized program backlog, and it supports final alignment during PI planning.

Figure 7-21. Continuous exploration activities
Continuous Integration
CI builds quality into the development process by continuously integrating the ongoing work of many Agile teams. All work is version controlled, and new functionality is developed and integrated into a full system or solution. It’s then validated in a suitable staging environment that ranges from cloud-based software systems to physical devices and device simulators.
SAFe describes four activities associated with continuous integration (Figure 7-22):
Develop describes the practices necessary to implement stories and commit the code and components into the trunk.
Build describes the activities needed to create deployable binaries and merge the development branches into the trunk.
Test end-to-end describes the methods necessary to validate the solution.
Stage describes the required practices to host and verify the system in a staging environment before production.

Figure 7-22. Continuous integration activities
Continuous Deployment
CD captures the processes associated with moving solutions through staging into production environments. As with continuous integration, this varies substantially based on the kinds of solutions created and their solution context. Ensuring solutions are ready for customers requires deployment and monitoring to provide flexibility in controlling releases, rolling back a version, or installing incremental updates and patches.
CD consists of four key activities in SAFe (Figure 7-23):
Deploy to production describes the practices necessary to deploy a solution to a production environment.
Verify the system represents the practices needed to make sure the changes operate in production as intended before they are made available to customers.
Monitor for problems describes the practices to monitor and report on any issues that may arise in production.
Respond and recover describes the activities to rapidly remedy any problems that happened during deployment.

Figure 7-23. Continuous deployment activities
Release on Demand
As we described, RoD is the ability to make new functionality available to customers all at once or incrementally based on market and business needs. SAFe describes four RoD practices (Figure 7-24):
Release describes how to deliver the solution to end users all at once or incrementally.
Stabilize and operate describes the process needed to make sure the system is working well from a functional and nonfunctional perspective.
Measure describes the practices necessary to quantify whether the newly released functionality provides the intended value.
Learn describes how to decide what should be done with the information gathered and prepare for the next loop through the CDP.

Figure 7-24. Four activities of RoD
RoD is critical to business agility, as the decisions of what to release to whom and when are vital business drivers. Release management provides governance for any upcoming scheduled or ad hoc releases. In a continuous delivery environment, participants closely monitor the release section of the program Kanban. This oversight ensures that items are released when needed to the right customers, that dark launches and canary releases are well managed, that hypotheses are evaluated, and that feature toggles are removed after production verification.
The Program Kanban
The program Kanban facilitates the flow of features through the CDP. Figure 7-25 illustrates a typical program Kanban with Work In Process (WIP) limits governing each state.
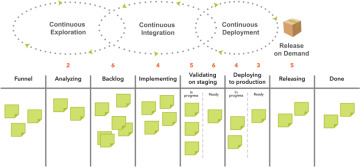
Figure 7-25. A typical program Kanban
New ideas begin with continuous exploration and may originate locally from the ART or an upstream Kanban system (e.g., solution or portfolio Kanban). Product Management and System Architects and Engineering manage this Kanban. The following states describe its flow:
Funnel. All new ideas are welcome here. They may include new functionality, enhancement of the existing system functions, or enabler work.
Analyzing. New ideas that align with the vision and support the strategic themes are further explored by Agile teams when they have available capacity. Analysis and refinement include the collaboration to turn an idea into one or more features with descriptions, business benefit hypotheses, acceptance criteria, and estimated story points.
Program backlog. The highest-priority features analyzed and approved advance to this state and await implementation. Feature estimates and acceptance criteria are also refined here.
Implementing. At every PI boundary, the ART pulls the top features from the program backlog and moves them into the implementing state. Through the PI planning process, they get split into stories, planned into iterations, and subsequently implemented by teams during the PI.
Validating on staging. During each iteration, features are integrated and tested with the rest of the system in a staging environment. Approved features move to the ‘ready’ part of this state, where they are prioritized again using WSJF and await deployment.
Deploying to production. When capacity becomes available for deployment activities (or immediately in a fully automated continuous delivery environment), the feature is moved to production. In systems that separate deployment from release, they are placed in the ‘ready’ part of this state. This state is WIP limited to avoid the buildup of features that are deployed but not yet released.
Releasing. When there is sufficient value, market needs, and opportunity, features are released to some or all the customers, where the benefit hypothesis can then be evaluated. Although the feature moves to the ‘done’ state, new work items may be created based on the learning gathered.
The Kanban system described here is a good starting point for most ARTs. However, it should be customized to fit the ART’s process, including the definition of WIP limits and the policies for each process state.
Program Epic Kanban System
ART initiatives that are simply too big to be completed in a single PI are called program epics. Also, some portfolio epics may need to be split into program epics to facilitate incremental implementation. Program epics may affect financial, human, and other resources that might be large enough to warrant a Lean business case, discussion, and financial approval from Lean Portfolio Management (LPM). Epics whose estimates exceed the established epic threshold will require review and approval.
Approving significant initiatives is one of the four critical Lean budget guardrails (see Chapter 9, Lean Portfolio Management, for more details).
Program Increment Roadmap
A PI roadmap is used to forecast the flow of work from the backlog (Figure 7-26). It consists of a series of planned PIs with identified milestones and releases. Each element on the roadmap is a feature scheduled to be completed within a particular PI. The PI roadmap may also reflect fixed-date and learning milestones occurring during that period. Releasing functionality can occur at any time during the PI.
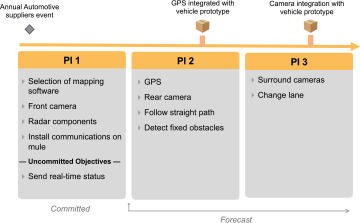
Figure 7-26. An example PI roadmap for an autonomous delivery vehicle
The roadmap in Figure 7-26 covers three PIs, which is typically sufficient to communicate a forecast to stakeholders, including the business and partners.
Market Rhythm and Events Inform the Roadmap
To create the highest value for all stakeholders, customer-centric organizations leverage market rhythms and market events to inform the roadmap.12 Simply put, the benefits of a solution can vary significantly based on when it’s released.
A market rhythm is a set of events that repeatedly occur on a predictable cadence. For example, retailers routinely prepare for the holiday shopping season by upgrading their systems to gain a competitive edge and to support significantly higher transaction volumes.
A market event is a one-time future event, which has a high probability of materially affecting one or more solutions. They can be external, such as the launch of government regulations, or they can be internally created, such as a company’s annual user conference.

