The Anatomy of a Digital Investigation
- A Basic Model for Investigators
- Understanding the Scope of the Investigation
- Identifying the Stakeholders
- The Art of Documentation
- Chapter Review
- Chapter Exercises
- References
This chapter will deal with the structural aspects that are common to most, if not all, digital investigations. Most current texts on the subject refer to a common investigation model, although there is some disagreement on how many components make up the model. This book will use a six-part model, which will be covered in more detail later in this chapter.
It is essential to understand at the outset precisely what the scope of the investigation entails. The type of investigation dictates the level of authorization required. Generally, there are three types of investigation. Internal investigations are sponsored by an organization. They generally start out as a deep, dark secret that the company doesn’t want getting out. Therefore, courts and state and federal agencies are rarely involved at the outset. The other two types—civil and criminal—both require involvement by the courts, but on different levels.
There will never be an investigation that does not have multiple stakeholders. In all court cases, there is the plaintiff and the defendant. In civil cases, these are the two litigants asking the courts to settle a dispute. In criminal cases, the defendant is the person accused of a crime and the plaintiff is the one making the accusation, which will always be some level of government authority. In addition to these obvious players, there are those on the sidelines whose interests must be considered. Lawyers will almost always be involved, and in cases that are likely to end up in court, be assured that the judge will take an active interest.
With people’s finances, freedom, or even lives at stake, the necessity for accurate and thorough reporting cannot be emphasized enough. It is so critically important that the subject of documentation will be discussed several times and in several places in this book. This chapter will start the reader off with the basics of good documentation.
Please be aware that this chapter deals only with the process of investigation. In Chapters 2 and 3, there will be detailed discussions of the various legal issues that the digital investigator must face on a daily basis. Consider the legal issues to be the glue that binds the model, but not the actual model. You can perform any number of investigations with no regard for the law. The results will be very revealing, but useless. Failure to be aware of legal aspects will cause the most perfectly executed investigation to fall apart the instant the case is picked up by the legal team.
A Basic Model for Investigators
Today’s teaching methods require everything to be broken down into a simplified structure that you can put into a diagram. Computer investigations are no different. Even though there will probably never be any two cases that are identical, they should always be processed in accordance with a standard investigative model. Kruse and Heiser (2001) laid out the basic computer investigation model in their book entitled Computer Forensics: Incident Response Essentials. Their model was a four-part model with the following steps:
- Assess
- Acquire
- Analyze
- Report
As shown in Figure 1.1, the four steps are further broken down into more granular levels that represent processes that occur within each step. A more thorough study expands the model to six steps, as follows:
- Identification/assessment
- Collection/acquisition
- Preservation
- Examination
- Analysis
- Reporting
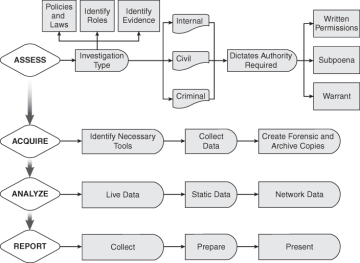
Figure 1.1 The steps of a digital investigation
The six-step model (Casey 2001) as seen in Figure 1.1 emphasizes the importance (and process) of preserving the data. It also distinguishes between the process of examination and analysis, whereas Kruse and Heiser considered them to be two parts of a single process. Experience has shown that acquisition and preservation are not the same, and while it might be an easy enough procedure to extract and examine data, accurate analysis is as much an art as it is a science.
From a management standpoint, each of these steps must be carefully monitored. Through a process of careful documentation of the history of each case, the various processes can be constantly reassessed for efficiency and reliability. When it becomes necessary, knowing what works and what doesn’t allows the observant manager to tweak the steps in order to improve organizational effectiveness.
Figure 1.1 emphasizes just how detailed these seemingly simple steps can actually be. The assessment phase alone has a multitude of steps involving people, hardware, environment factors, political implications, and jurisdiction. Acquisition of evidence cannot begin until all potential sources of evidentiary material are identified, collected, inventoried, and catalogued. All of this must be done according to strict legal guidelines, or any subsequent investigation will be a waste of time. Legal and internal regulations regarding privacy must be followed at all times, or any information collected will not be admissible as evidence should the case ever make its way to court. In the case of internal investigations, adherence to corporate guidelines will generally be sufficient.
Identification/Assessment
Before beginning any investigation, the general rules of engagement must be established in advance and from the very start be strictly followed. Those rules can be very different between criminal and civil cases. It is essential that the investigator know what regulations apply to a specific investigation in order to not damage or destroy a case by failure to abide, either flagrantly or inadvertently.
In a criminal investigation, it is almost always necessary to obtain a warrant before seizing systems, media, or storage devices. In order to obtain that warrant, the investigating entity must provide a judge sufficient evidence that a crime has been committed, is about to be committed, or is in the process of commission. The specific type of information sought by the investigation must be identified; general fishing expeditions are never approved by a reputable judge—at least not for the purpose of issuing warrants.
Civil cases have more lenient guidelines. Internal investigations sponsored by an organization can be even more lenient. Federal guidelines regarding invasion of privacy are not as strictly enforced on civilian investigators looking into civil infractions as they are on agents of a government—state, federal, or local—who are investigating criminal complaints. Internal investigations can be made even easier when employees or members have signed a statement outlining an organization’s policies and guidelines.
No case should be accepted by an investigator directly. An executive-level decision, based on a set of predefined guidelines (to be discussed later), must be made on whether to accept or decline each individual case presented to the organization. While it falls upon a law enforcement agency to accept any case assigned that involves violation of state or federal statutes, a private organization can refuse to accept cases for a variety of reasons. The organization’s leadership must indentify the criteria for case acceptance and stick to those criteria. It does the company’s reputation no good to be associated with a pedophile after publicly stating that its motives are to defend the community.
Make a list of all legal documentation that will be required. Warrants will be required in criminal cases. Court orders or subpoenas will be needed in civil matters. Signed agreements outlining the scope of the investigation should be required in all internal investigations.
Once the ground rules are established, it is time to identify potential sources of evidence. The obvious place to look is on the local system, including hard disk drives, removable media that might be lying about, printers, digital cameras, and so forth. Less obvious sources of information might be PDAs, external hard disks or optical drives, and even system RAM if the data processing systems are still running when the incident is reported. Knowing in advance what must be acquired can prevent the investigator from making critical errors during the process of acquisition.
Collection/Acquisition
This is the most technical part of the investigation and can also be the most critical time for making errors. If the case under scrutiny should ever come to trial, the investigator presenting the case must be able to prove the following:
- The data is authentic.
- The copy of the data used for analysis is reliable.
- The data was not modified during acquisition or analysis (chain of custody).
- The tools used to analyze the data are valid tools.
- Sufficient evidence, both incriminating and exculpatory, has been acquired and analyzed to support the proffered conclusion.
- The conclusions drawn are consistent with the data collected and analyzed.
- People involved in the collection and analysis of the data are properly trained and qualified to do their job.
This doesn’t sound easy, and it isn’t. Details on how to assure that all of these requirements are met are covered in greater detail in later chapters. For now, suffice it to say that it is essential that they be fulfilled.
Preservation
A cardinal rule of digital investigation is that the original data must never be touched. For many years, the standard rule has been that a forensically sound copy of the original be made and that the examination and analysis of data be performed on the forensic copy. In terms of nonvolatile media, such as hard disks, removable media, and optical disks, this is still the rule. Devices should always be mounted as read-only in order to assure that no data is modified or overwritten during the process of mounting the device. Hard disk duplicators are designed specifically for this purpose, and in Windows systems, a simple modification of the registry allows USB devices to mount read-only.
Legal issues might arise if there is any possibility that media used to store images may have been contaminated. Be aware of that possibility and either have new media available for collection or be certain that previously used media has been forensically wiped.
In many cases, it becomes essential that copies of data be acquired through a process of live acquisition. This is the case when it becomes necessary to capture the contents of memory from a running system, to acquire log files from network devices that cannot be brought down, or to archive information from network servers or storage appliances that defy the making of a forensic copy. If it is not possible, for any reason, to create a forensically sound copy, it is essential that the investigator document the reasons such a copy could not be made and record as accurately as possible the state of the evidentiary source before and after acquisition.
Storage of preserved information becomes part of the chain of custody process, and care must be taken that all data and devices collected during this phase are properly documented and tracked. Be able to verify that there was never a possibility for evidence to become tainted through outside tampering, corruption, or improper procedure.
Examination
The process of examining data increases in scope and complexity every year. Whereas 1.44MB floppy disks were once the repository for stolen and illicit data, investigators these days are presented with flash drives the size of key fobs that hold 64 or more gigabytes of data and hard disks that store in excess of a terabyte. To make matters worse, the data is not likely to sit on a porch swing in plain view for anyone to see. Investigators will find it necessary to look for evidence in unallocated space left behind by deleted files. Hidden partitions, slack space, and even registry entries are capable of hiding large quantities of data. Steganography can hide documents inside of an image or music file. So essentially, the investigator is given an archive the size of the Chicago Public Library and asked to find a handwritten note on the back of a napkin tucked somewhere inside of a book.
Data carving tools and methods of looking for evidentiary material have evolved, and depending on the nature of the case, the investigator’s tool kit will require having several utilities. For criminal cases requiring forensically sound presentation, it is critical that the tools used to examine data be those considered valid by the courts. There are a few commercially available software suites approved for evidentiary use. Among these are Encase by Guidance Software and the Forensics Tool Kit (FTK) from Access Data Corporation. A suite of tools running on Linux that is not “officially” sanctioned but is generally considered acceptable by most courts is The Sleuth Kit, designed by Brian Carrier.
Keeping up with technical innovations in the industry is most critical in this area. As new technology emerges, new tools will be needed to examine the accumulated data it creates. The organization that follows the cutting edge of technology will always be two steps behind those that help develop it. The balancing act comes when management must defend the use of a new tool to which the courts and lawyers have not yet been exposed. Be prepared to defend the tool along with the conclusions it helped you formulate.
Analysis
Here is where the process of digital forensic investigation leaves the realm of technology and enters that of black magic. It is up to the investigator to determine what constitutes evidence and what constitutes digital clutter. A variety of tools exist that assist the investigator in separating OS files from user data files. Others assist in identifying and locating specific types of files.
Technique is as critical as the selection of tools. For example, when searching an e-mail archive for messages related to a specific case, string searches can bring up all those that contain specific keywords. Other utilities can detect steganography or alternate data streams in NTFS file systems. Collecting the data necessary to prove a case becomes as much art as it is science. One thing that the investigator must always keep in mind is that exculpatory evidence must be considered as strongly as incriminating evidence.
Reporting
Documentation of the project begins the minute an investigator is approached with a potential case. Every step of the process must be thoroughly documented to include what people are involved (who reported what, who might be potential suspects, potential witnesses, or possible sources of help), as well as thorough documentation of the scene, including photographs of the environment and anything that might be showing on computer monitors. Each step taken by the investigator needs to be recorded, defining what was done, why it was done, how it was done, and what results were obtained. Hash files of data sources must be generated before and after acquisition. Any differences must be documented and explained. Conclusions drawn by the investigating team must be fully explained. On the witness stand, it is likely that an investigator will be required to prove his or her qualifications to act as an investigator. A meticulously investigated case can be destroyed by inadequate documentation. While commercial forensic suites automate much of the documentation process, there is still much manual attention required of the investigator.