Securing Massive IoT Deployments in 5G
- Massive IoT–Based Threats in 5G
- Securing mIoT Deployments in 5G Networks
After reading this chapter, you should have a better understanding of the following topics:
Threats in massive IoT use case deployments
Securing massive IoT networks
Real scenario case study examples of massive IoT threat surfaces and threat mitigation techniques
This chapter will take you through the threat surfaces in 5G massive IoT deployments and mechanisms to mitigate the threats.
This chapter will be of particular interest to the following teams from enterprise, industry verticals, Non-Public Networks (NPN), 5G service providers deploying 5G mIoT, and cybersecurity vendors planning product developments and new functionalities to secure 5G mIoT use cases.
Mobile infrastructure strategy teams of service provider deploying mIoT in 5G
Security strategy teams within service provider and enterprise verticals planning on deploying 5G mIoT
Transmission and the packet core team within service providers and private 5G enterprises planning to deploy 5G mIoT
Cloud computing and data center teams involved with 5G strategy and deployment
Security architects and design teams looking at securing the public and non-public mobile infrastructure
Solution and security architects deploying 5G mIoT on enterprises and industry verticals
Enterprise solution and security architects using IoT services from mIoT service provider
Government departments deploying 5G mIoT
Cybersecurity vendor teams looking to secure mIoT deployments for their customers
Product managers of cybersecurity vendors trying to identify use cases for new products or features to protect 5G mIoT deployments
5G represents a disruptive shift from just traditional consumer smartphones to advanced enterprise services, including ultra-reliable low-latency communication (URLLC)–based machine-to-machine (M2M) use cases. 5G is expected to be widely adopted in enterprise, industrial, and IoT use cases, enabling greater workforce mobility, automation, and countless new applications. Incorporation of 5G into these environments requires a deeper level of integration between end-user networks and 5G service interfaces, exposing both enterprise owners (in particular, operators of critical information infrastructure) and 5G service providers to new risks. Before we get into the risks and mitigation of risks, we will first need to look into the types of IoT use cases.
5G also sees a departure from the reliance on a single approach to authenticating all users onto the network-based SIM cards. The Third-Generation Partnership Project (3GPP) has addressed such shortcomings, with 5G now integrating the Extensible Authentication Protocol (EAP) framework, first adopted by Wi-Fi into WPA-Enterprise back in 2002, into its architecture. The 5G standard now provides examples of how to use EAP-TLS certificate-based authentication in 5G as well as other EAP methods that support mutual authentication. The list that follows outlines some of the key reasons why IoT threats are quite critical in 5G based on the excerpts taken from the Cisco Annual Internet Report (2018-2023):
The number of devices connected to IP networks will be more than three times the global population by 2023. There will be 3.6 networked devices per capita by 2023, up from 2.4 networked devices per capita in 2018. There will be 29.3 billion networked devices by 2023, up from 18.4 billion in 2018.
Globally, devices and connections are growing faster (10 percent compound annual growth rate [CAGR]) than both the population (1.0 percent CAGR) and the Internet users (6 percent CAGR). This trend is accelerating the increase in the average number of devices and connections per household and per capita. Each year, various new devices in different form factors with increased capabilities and intelligence are introduced and adopted in the market. A growing number of M2M applications, such as smart meters, video surveillance, healthcare monitoring, transportation, and package or asset tracking, are significant contributors to the growth of devices and connections. By 2023, M2M connections will constitute 50 percent of the total devices and connections.
M2M connections will be the fastest-growing device and connections category, growing nearly 2.4-fold during the forecast period (19 percent CAGR) to 14.7 billion connections by 2023.
With this type of growth in the number of devices and spurts in new use cases such as M2M, an attack that successfully disrupts the network, or that steals or undermines the integrity of confidential data, could have a far greater economic and societal impact than previous generations.
IoT devices and applications have been around for quite some time and are not a new concept for 5G. There are networks today using LTE or NB-IoT technologies enabling IoT use cases. 5G offers flexibility in IoT deployment. The use cases aimed at 5G IoT are devices having different bandwidth requirements. Some require high bandwidth and transmit in burst, while some require low bandwidth and continuous connectivity. 5G offers this capability to support the massive number of devices with different bandwidth requirements. In addition, 5G also supports enterprise and industry use cases that have strict requirements on latency. This is one of the key reasons why the industry is looking at adopting 5G. The flexible mode of 5G deployment using network slicing and deployment of applications in the edge of the network can bring down the latency to 1ms or less, enabling ultra-reliable and low-latency use cases such as factory automation, enhanced vehicular technologies such as vehicle-to-everything (V2X), power and utility sector use cases such as smart energy grids, and other demanding use cases to become a reality.
There are different types of IoT use cases in 5G depending on the data consumption, energy consumption, and scale of deployment. When you take a step back and look at the use-case scenarios in 5G, we can split the IoT devices into smart devices and not-so-smart devices. Smart IoT devices are the devices that have some intelligence built into them and can make some decisions based on the input data. The not-so-smart IoT devices are the devices that just send the collected data and receive certain actions, such as stop data collection and a query to start data collection.
Use cases attributed to 5G such as smart cities would require the use of both types of devices, as shown in Figure 8-1, and have an artificial intelligence (AI), machine learning (ML), and an analytics layer to analyze the information from multiple devices and make a decision based on it. An example could be automated car parking in a busy area such as an airport parking lot, as shown in Figure 8-1.
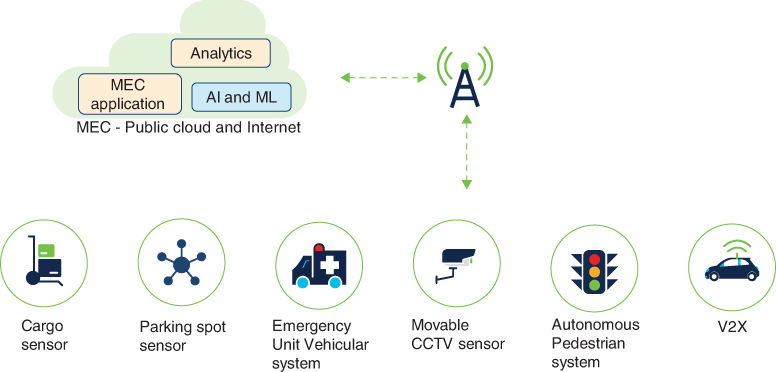
FIGURE 8-1 Different IoT Device Types to Enable a 5G Smart City
As shown in Figure 8-1, it would require different types of mIoT devices to enable the smart city use case. Table 8-1 lists the types of devices to fulfill the use case of finding a parking spot and the safest way to reach the parking spot.
TABLE 8-1 Different IoT Device Types
IoT Device |
mIoT Device Type |
Function |
|---|---|---|
Cargo sensor |
Not-so-smart device |
Sends the geo-location metadata along with the speed |
Parking spot sensor |
Not-so-smart device |
Indicates whether or not a vehicle is located in a parking spot |
Emergency Unit Vehicular system |
Not-so-smart device |
Indicates whether an emergency vehicle is active in the location |
Movable CCTV sensor |
Not-so-smart device |
Detects if there is movement near the parking spot |
Autonomous pedestrian system |
Smart device |
Indicates any V2X application in the vicinity and broadcasts a message based on whether or not a pedestrian is crossing. Captures any speeding instances and sends data to the road safety officers. Indicates any collision and immediately broadcasts messages to the emergency health unit. |
V2X |
Smart device |
Provides a road safety application such as intersection movement assist, provides emergency brakes, and also includes V2V (vehicle-to-vehicle) communications |
As listed in Table 8-1, to fulfill this example of smart city–based parking, there is a need for both not-so-smart-devices and smart devices.
In this example, the cargo sensor, Emergency Unit Vehicular system, and autonomous pedestrian system are all part of the collision-prevention mechanism. The parking spot sensor and movable CCTV sensor are part of the parking detection mechanism. The V2X system is embedded within the vehicle for passing along the metadata to the MEC application.
All the data from the mIoT devices is then passed on to the AI and ML system and real-time (RT) analysis system. The AI, ML, and analytics system will then detect the free parking spot and the safest way to approach the parking spot and then help park the car or indicate the parking spot and the best way to reach it.
Massive IoT in 5G addresses the need to support billions of connections with a range of different services. IoT services range from device sensors requiring relatively low bandwidth to connected cars that require a similar service to a mobile handset. Network slicing provides a way for service providers to enable services to enterprises, giving them the flexibility to manage their own devices and services on the 5G network. mIoT, as the name suggests, is a category of use cases that is driven by scale.
Figure 8-2 illustrates an example of components that are part of the mIoT deployment.
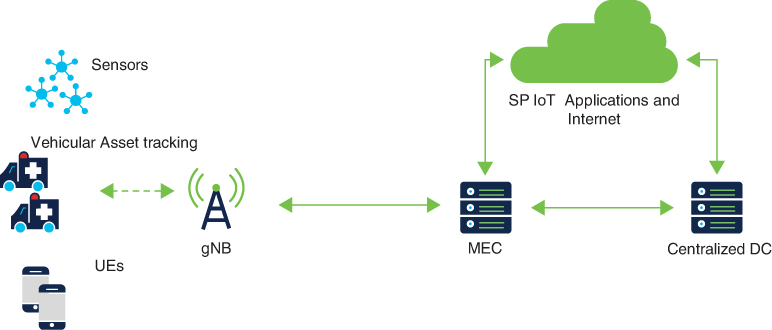
FIGURE 8-2 mIoT Deployment in 5G
Figure 8-2 shows an example of mIoT use-case deployment using 5G. The gNB serves geographically disparate devices such as sensors and vehicles that need to be tracked. mIoT would typically include devices that transmit and consume low data and are in the scale from hundreds to millions. Depending on the device type, it could be low-energy-consuming devices with limited access to power with a very light software stack for communications. There are device vendors in the market with 5G-capable chips with optimized power consumption.
This chapter will cover the 5G MIoT part. 5G IoT use cases based on smart devices (V2X, smart city, industrial IoT use cases, and so on) are covered in Chapter 9, “Securing 5G Use Cases.”)
Massive IoT–Based Threats in 5G
Figure 8-3 shows the key threats for the device-based threats for the devices connecting to the service provider’s 5G infrastructure. The devices in this case can be the 5G user equipment (UE), sensors, and IoT devices connecting to the 5G network provided by the service provider.
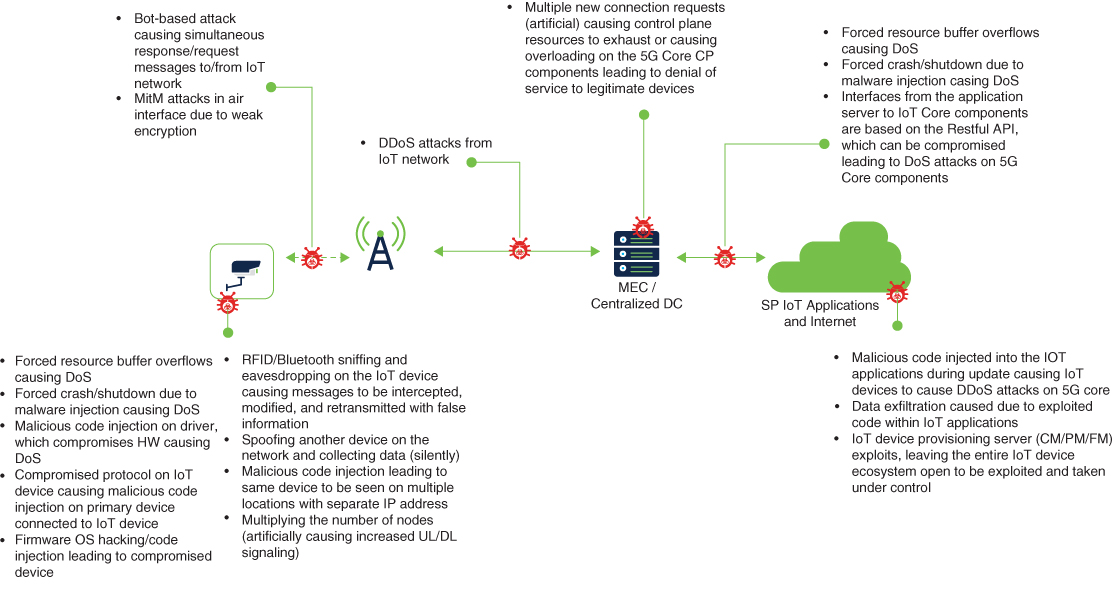
FIGURE 8-3 mIoT Threat Surface in 5G Deployments
Figure 8-3 shows 5G multi-access edge compute (MEC), centralized 5GC (5G Core), public or private cloud-based SP applications, and the Internet access layer. Depending on the deployment plans of the service provider, the 5G User Plane Function (UPF) would be deployed in the MEC, along with any of the IoT applications that require caching. When the UPF network functions are deployed in the MEC, the N6 interface—the interface between the data network (DN) and the UPF—is also configured to allow UE and 5G devices to interconnect with the data network. Depending on the deployment scenario, the 5GC could host the 5G network functions that have low impact with higher latency, such as control plane functions, user plane functions for some IoT use cases, and the operations, administration, and maintenance (OAM) functions. Many service providers are also planning to have the configuration management (CM), fault management (FM), and performance management (PM) for the consumer IoT devices being catered to from the public/private cloud.
The majority of the threat surfaces illustrated in Figure 8-3 are primarily due to the device vulnerabilities and the devices being compromised by the command and control (C&C) server.
Here are some of the key threats related to mIoT use cases within the 5G networks:
C&C-based attacks
Malicious code injection on the driver that compromises the hardware, causing a denial of service (DoS)
Forced resource buffer overflows causing DoS
Forced crash/shutdown due to malware injection, causing DoS
Compromised protocol on an IoT device, causing malicious code injection on the primary device connected to the IoT device
Firmware OS hacking/code injection, leading to a compromised device
Radio-frequency identification (RFID)/Bluetooth sniffing and eavesdropping on the IoT device, causing messages to be intercepted, modified, and retransmitted with false information
Spoofing another device on the network and exfiltrating data
Malicious code injection leading to the same device being seen at multiple locations with separate IP addresses
Multiplying the number of nodes (artificially), causing increased signaling in both UL/DL
Device Vulnerabilities Due to Weak Built-in Security
mIoT devices usually have very weak built-in security mechanisms due to lower price points of the devices to make them affordable to a large consumer base. The IoT deployment of any type, be it based on smart IoT devices or not-so-smart IoT devices, needs to be catered to by robust security controls to mitigate the vulnerabilities introduced by weak built-in security mainly due to the low cost and limitations due to the form factor. Non-mIoT use cases that are not geographically located would also need multilayered security controls to secure them from targeted attacks very specific to industry verticals, such as major automotive manufacturers or government utility verticals.
Spoofing, cloning, and eavesdropping on the 5G endpoints/IoT devices can be carried out by attackers impersonating an RFID or Bluetooth device and reading and recording the transmitted data from the 5G-enabled IoT device. This is primarily made possible due to weak access controls and poor authentication methods used by the IoT device. These kinds of attacks are more prevalent in verticals of IoT such as healthcare where the IoT devices use Bluetooth to transfer the patient’s health statistics to a tablet where the vital stats of the patient can be checked/monitored by the healthcare workers.
Another type of attack mentioned in Figure 8-3 is where the devices are compromised. In this instance, all the data from the impacted devices is dropped or redirected instead of being transmitted to the intended receiver for further forwarding or analysis. The data from such devices can then be analyzed by the attacker for any valuable data points, such as the IP address of the receiver, which can then be targeted for DoS.
These kinds of attack methods can also be referred to as sinkhole attacks or a form of routing attack. This is because the method of attack used in such instances is to route the packets away from the main intended receiver. To prevent the detection of such attacks, the data can be mirrored to the malicious data collection server using a method very similar to port mirroring or Switch Port Analyzer (SPAN), which is used quite commonly in the network monitoring environment of the service provider networks. SPAN copies (or mirrors) traffic received or sent (or both) on source ports or source VLANs to a dedicated destination switch port for analysis. You can analyze network traffic passing through switch ports or VLANs by using SPAN or Remote SPAN (RSPAN) to send a copy of the traffic to another port on the switch or on another switch that has been connected to a network analyzer or other monitoring solution.
Management layer–based attacks are another key concern for device-based attacks within 5G. In these attacks, the attacker tries to take control of the key management layers, such as CM, FM, and PM, by exploiting the existing vulnerabilities of the IoT vendors’ management platform or the open source components used in the vendors’ IoT platform. Once the vulnerability has been successfully exploited, the attacker gains access and control over all endpoints catered for by the IoT vendor for the service provider. This can now be used for DoS and distributed denial-of-service (DDoS) attacks. One of the methods the attacker could also use here is to change the encryption type or level (from encrypted to null encryption), which makes the entire IoT network susceptible to man-in-the-middle (MitM) attacks.
The key threat surfaces and vulnerabilities are discussed in more detail in the sections that follow.
Supply Chain Vulnerability
Supply chain vulnerability is a well-known issue across different industry segments. The challenge of supply chain vulnerabilities becomes more prominent in 5G, as it enables attaching millions of low-cost IoT devices to the network. 5G also introduces critical infrastructure–based use cases and caters for use cases like smart cities, defense, and so on. These critical infrastructure 5G IoT use cases attract more nation-state attackers and thus are under higher levels of risk for cyberattacks. Supply chain is one of the weak links in security. If not secured properly, it opens the door wide for attacks, and the impacts of the attacks could be devastating, depending on the use case where the vulnerable IoT device was used. This section will take you through the vulnerabilities in the IoT supply chain related to manufacturing and distribution, as shown in Figure 8-4.
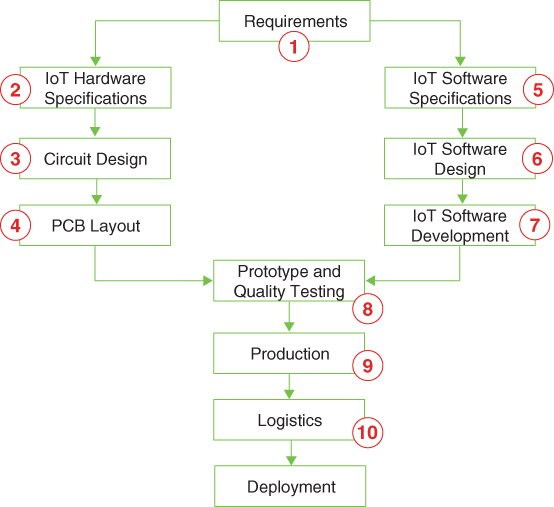
FIGURE 8-4 Vulnerabilities in Different Stages of the Supply Chain
Key vulnerabilities and threat vectors for the IoT supply chain related to manufacturing and distribution are explained in the list that follows:
The requirement stage is when you send the requirements for your IoT device to the vendor. This will include details like maximum energy consumption, dimension of the unit, maximum/minimum temperature, pressure (depending on use case), software or platform requirements such as integration options using API, and so on. The threat vector here is the requirement that is actually passed on to the vendor product R&D and manufacturing team. An attacker might add a couple of details in the requirements not actually requested by you. These newly added details are aimed at creating the backdoor using hardware or software remodifications to the original design, which can then be exploited by the attacking entity once deployed.
The hardware specification team would normally take the requirements from the customer and map them to the required hardware, including deciding what sort of components should be used in manufacturing the device. Typical considerations are values to withstand humidity, temperature, power consumption, and so on. The threat vector here is that an attacker could choose certain components that will fail when a certain condition is met. For example, the malicious actor or the attacking entity could intentionally choose a substandard electronic component or a customized component that fails after a certain temperature or humidity level is reached.
Once the components are finalized, the design team would make a schematic of the design that will be used as a blueprint for the printed circuit board (PCB) manufacturing for the IoT device. This is a very important part of the manufacturing process, as all the further checks on quality and so on would be referred back to the schematic. The attacking entity or the malicious actor could alter the design to include an eavesdropping component to leak sensitive data to a predetermined destination such as a C&C server.
The PCB layout process and component soldering are the next steps after the circuit design process. Here, the key vulnerabilities and threat vectors are due to the attacker choosing counterfeit electronic components causing intermittent failures that are difficult to find and correct.
IoT software specifications are taken from the requirements list you have provided to the IoT vendor/manufacturer. A member of the IoT software specification team or an attacker working in the software specification team could be directed to modify the specification for the software. The software specification will also be used in the software quality process for validating the software and to ensure that the designed software meets the software specifications. Any modification done in the software specification process will be considered as the software blueprint for the device.
The software design team would follow the specifications set by the software specifications team and specify the architecture and software technology to be used. In this process, the vulnerabilities are mainly due to the lack of knowledge about security leading to weak software for the device.
The software development team programs the IoT device with the chosen software language. With attacks aimed at software vulnerabilities on the rise, it is imperative that the software team follows secure software design and avoids known vulnerabilities such as buffer overflows, which occur when there is more data in the buffer than it can handle, leading to software crash and thus creating a point for cyberattack. This can be intentionally implemented by an attacker within the software development team. Another threat vector is when a team member of the software development team is instructed by an attacker or an attacking entity to include malicious code within the program to allow a backdoor entry to the device or to the private network where the IoT device is deployed.
In the post-PCB layout and software development process, the IoT device manufacturer would validate whether the hardware prototype and software fulfill the requirements set by your (or your customer’s) IoT device requirement. This is the last part of the process when a vulnerability can be identified and patched. If the quality team is compromised by an attacker, the specific vulnerability that is planned to be exploited by the attacker/attacking entity will be overlooked and will not be patched. This will leave the IoT device open for any attacks.
One of the key vulnerabilities in production is shadow production. Shadow production is where the real production numbers are hidden and used to flood the market with IoT devices with backdoors and vulnerabilities, making the devices open to attacks. Another threat vector is where the Joint Test Access Group (JTAG) ports are left unsecured. JTAG is an interface that provides an option for debugging, reprogramming, and so on. In many gaming consoles, the JTAG ports are unsecured and open to user access. If you had the common interface cable for JTAG, you could plug it into your computer, use manufacturer default credentials, and play pirated games with some modifications on the attributes using the JTAG ports. The same unsecured JTAG port in an IoT device can allow an attacker to have unauthorized access and possibly have access to the private network where the IoT devices are deployed. The physical attacks, such as injecting malicious code into the IoT network, can be made possible by tampering with an IoT endpoint, gaining control over it, and then using that endpoint to gain access into the central IoT network. Attackers also exploit the JTAG interface used by manufacturers for debugging purposes. JTAG is an industry standard for on-chip instrumentation in electronic design automation (EDA). JTAG is also used to program field-programmable gate arrays (FPGAs). Most CPU vendors still use JTAG for debugging purposes. If JTAG ports are left unprotected, this interface can become a critical attack vector on the system.
Logistics is the other vulnerability in the supply chain that is prone to sabotage or modification of the IoT devices while in transit. Though this is not the most preferred attack vector for IoT devices in the supply chain, for critical infrastructure use cases, logistics needs to be carefully monitored. Your supply chain risk management (SCRM) should ensure that you have the right controls, such as choosing validated and security-cleared logistics vendors for shipping and transportation of IoT devices from production to deployment.
The attacks are primarily aimed at data exfiltration, tampering with the files within the IoT network, and gathering information. With the control garnered over the IoT network, the attacker could control the operations and the data flow between the IoT network and the 5G network components, such as a radio (gNB) or storage/configuration in the MEC layer of the 5G network. With the control over the IoT network, the attackers can damage the IoT devices and disrupt the IoT service, thereby causing DoS to service providers’ IoT services. This is not a new threat vector for 5G technology specifically; it is prevalent in legacy technologies such as 2G, 3G, and 4G, but it’s critical for 5G technology, as it is aimed at enabling IoT use cases such as mIoT that would impact different government and private sectors.