- 3.1 5G Use Cases
- 3.2 NGMN 5G Architecture Framework
- 3.3 3GPP 5G Architecture
- 3.4 Key Terms and Review Questions
- 3.5 References and Documents
3.2 NGMN 5G Architecture Framework
NGMN introduced a framework for the 5G architecture in its 2015 white paper and subsequently elaborated the framework in a later document, 5G End-to-End Architecture Framework (August 2019). The NGMN framework emphasizes the need for modular network functions that could be deployed and scaled on demand to accommodate various use cases in an agile and cost-efficient manner. The NGMN approach is built on the concept of the softwarization of 5G networks. In essence, softwarization is an overall approach for designing, implementing, deploying, managing, and maintaining network equipment and/or network components through software programming.
Four approaches to softwarization are important in 5G networks and reflected in the NGMN model:
Software-defined networking (SDN): An approach to designing, building, and operating large-scale networks based on programming the forwarding decisions in routers and switches via software from a central server. SDN differs from traditional networking, which requires configuration of each device separately and relies on protocols that cannot be altered. Chapter 7, “Software-Defined Networking,” covers SDN.
Network functions virtualization (NFV): The virtualization of compute, storage, and network functions by implementing these functions in software and running them on virtual machines. Chapter 8, “Network Functions Virtualization,” covers NFV.
Edge computing: A distributed information technology (IT) architecture in which client data is processed at the periphery of the network, as close to the originating source as possible.
Cloud-edge computing: A form of edge computing that offers application developers and service providers cloud computing capabilities as well as an IT service environment at the edge of a network. The aim is to deliver compute, storage, and bandwidth much closer to data inputs and/or end users. Chapter 10, “Multi-Access Edge Computing,” covers cloud-edge computing.
Layered Functionality
Figure 3.4 illustrates the NGMN architecture framework. The architecture comprises three layers and an end-to-end (E2E) management and orchestration entity.
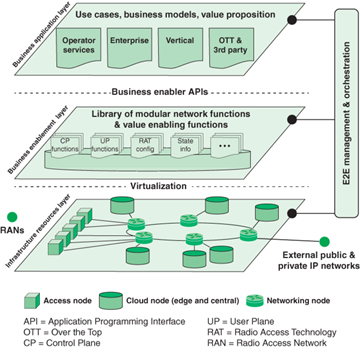
FIGURE 3.4 5G Architecture (NGMN)
The infrastructure resource layer consists of the physical resources and system software of a fixed-mobile converged (FMC) network. Figure 3.4 shows in detail the core network portion, which includes these types of devices:
Cloud nodes: These nodes provide cloud services, software, and storage resources. There are likely to be one or more central cloud nodes that provide traditional cloud computing service. In addition, cloud-edge nodes provide low latency and higher-security access to client devices at the edge of the network. All of these nodes include virtualization system software to support virtual machines and containers. NFV enables effective deployment of cloud resources to the appropriate edge node for a given application and given fixed or mobile user. The combination of SDN and NFV enables the movement of edge resources and services to dynamically accommodate mobile users.
Networking nodes: These are IP routers and other types of switches for implementing a physical path through the network for a 5G connection. SDN provides for flexible and dynamic creation and management of these paths.
Access nodes: These provide an interface to radio access networks (RANs), which in turn provide access to mobile user equipment (UE). SDN creates paths that use an access node for one or both ends of a connection involving a wireless device.
Hardware and software resources at the infrastructure resources layer are exposed to higher layers and to the end-to-end management and orchestration entity through relevant application programming interfaces (APIs). Performance and status monitoring as well as configurations are intrinsic parts of such an API.
The business enablement layer is a library of all functions required within a converged network in the form of modular architecture building blocks, including functions realized by software modules that can be retrieved from the repository to the desired location, and a set of configuration parameters for certain parts of the network (e.g., radio access). The functions and capabilities are called upon request by the orchestration entity, through relevant APIs. For certain functions, multiple variants might exist. For example, there may be different implementations of the same functionality that have different performance or characteristics. The different levels of performance and capabilities offered could be utilized to differentiate the network functionality much more than in today’s networks (e.g., to offer mobility functions such as nomadic mobility, vehicular mobility, or aviation mobility, depending on specific needs). Specific types of components at this layer include:
Control plane functions: These are modules that implement the control signaling functions within the network, as well as control signals associated with SDN and NFV.
User plane functions: These modules deal with the exchange of user data over a connection.
Radio access technology (RAT) configuration: These functions facilitate the configuration of elements in the RAN, including base stations.
State information: State information is split from functions and nodes and managed separately. This includes the state of network connections and RAN radio channels.
With the use of SDN and NFV, 5G networks can support flexible functions and capabilities. The functions at the business enablement layer can tailor connections, configurations, and resource deployment for each use case.
The business application layer contains specific applications and services that support the following users of the 5G network:
Mobile network operator: A mobile network operator is a wireless telecommunications organization that provides wireless voice and data communication for its subscribed mobile users. The operator owns or controls the complete telecom infrastructure for hosting and managing mobile communications between the subscribed mobile users with users in the same and external wireless and wired telecom networks, including radio spectrum allocation, wireless network infrastructure, backhaul infrastructure, billing, customer care, provisioning computer systems, and marketing and repair organizations. Mobile network operators are also known as wireless service providers, wireless carriers, and cellular companies.
Enterprise: An enterprise is a business that offers services over the mobile network. These services include applications that run on mobile devices and cloud-based services that enable application portability across multiple devices.
Verticals: An industry vertical is an organization that provides products and/or services targeted to a specific industry, trade, profession, or other group of customers with specialized needs. A vertical might provide a range of products or services useful in the banking industry or healthcare. In contrast, a horizontal provides products or services that address a specific need across multiply industries, such as accounting or billing products and services. Some 5G use cases are realized by standalone private networks managed by the vertical industry itself rather than the network service provider (NSP). A good example is factory automation. In such cases, the vertical can own and control its own application packages and business application layer.
Over-the-top (OTT) and third parties: OTT or third-party services can be defined as any services provided over the Internet and mobile networks that bypass traditional operators’ distribution channel. Cooperation between the mobile network operator and the OTT involves providing quality of service (QoS) and latency attributes in network slices. Examples of OTTs include:
Voice over Internet Protocol (VoIP): Skype, Viber, etc.
Short Message Service (SMS): WhatsApp, Kakao Talk, Line, Telegram, etc.
Apps: Search portals, news portals, banking, weather, shopping, etc.
Cloud services: Dropbox, Google Drive, Apple iCloud, etc.
Internet television (video streaming): Netflix, Hulu, YouTube, Amazon Video, etc.
At the interface to the end-to-end management and orchestration entity, users at the business application layer can build dedicated network slices for an application or map an application to existing network slices.
The E2E management and orchestration entity is the contact point to translate the use cases and business models into actual network functions and slices. It defines the network slices for a given application scenario, chains the relevant modular network functions, assigns the relevant performance configurations, and finally maps all of this onto the infrastructure resources. It also manages scaling of the capacity of those functions as well as their geographic distribution. In certain business models, it could also possess capabilities to allow for third parties to create and manage their own network slices.
Network Slicing
Chapter 2 introduces the concept of network slicing. Figure 2.11 suggests that slices can divide classes of internal network functions, such as dividing eMBB from mMTC from URLLC. The NGMN framework suggests that slices could effectively partition networks in such a way that different classes of user equipment, utilizing their respective sets of radio access technologies, would perceive quite different infrastructure configurations, even though they would be accessing resources from the same pools.
NGMN defines a network slice as being composed of a collection of 5G network functions and specific RAT settings combined together for the specific use case or business model. Thus, a 5G slice can span all domains of the network—software modules running on cloud nodes, specific configurations of the transport network supporting flexible location of functions, and a dedicated radio configuration or even a specific RAT—as well as configuration of the 5G device.
Figure 3.5 illustrates three use cases highlighted in the NGMN white paper. The blacked-out core network resources represent resources not used to create the network slice.
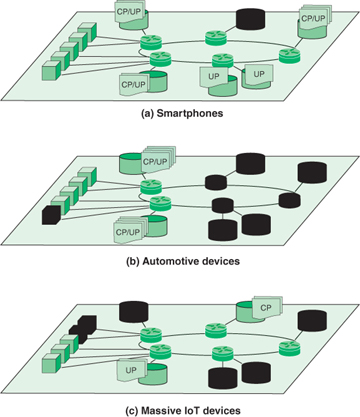
FIGURE 3.5 5G Network Slices Implemented on the Same Infrastructure
Cloud nodes that are part of the slice may include the following:
Control plane (CP) functions associated with one or more user plane (UP) functions (e.g., a reusable or common framework of control)
Service- or service category–specific control plane and user plane function pairs (e.g., user-specific multimedia application session)
The first network slice depicted in Figure 3.5 is for a typical smartphone use case. Such a slice might have fully fledged functions distributed across the network. The second network slice in Figure 3.5 indicates the type of support that may be allocated for automobiles in motion. This use case emphasizes the need for security, reliability, and low latency. A configuration to achieve this would limit core network resources to nearby cloud edge nodes, plus the recruitment of sufficient access nodes to support the use case. The final use case illustrated in Figure 3.5 is for a massive IoT deployment, such as a huge number of sensors. The slice can contain just some basic CP and UP functions with, for example, no mobility functions. This slice would only need to engage the access nodes nearest the IoT device deployment.
Thus, as Figures 3.4 and 3.5 suggest, a layered architecture with emphasis on softwarization provides the flexibility needed to fully exploit the 5G infrastructure.
