Data Breach - Crisis Management
- 3.1 Crisis and Opportunity
- 3.2 Crisis Communications, or Communications Crisis?
- 3.3 Equifax
- 3.4 Conclusion
Data breaches are crises and should be managed accordingly. The traditional NIST incident response model has limited value when a data breach rears its ugly head. Using an Equifax breach as a case study, Sherri Davidoff introduces a crisis management model and shows how it applies to data breaches.
Save 35% off the list price* of the related book or multi-format eBook (EPUB + MOBI + PDF) with discount code ARTICLE.
* See informit.com/terms
On September 7, 2017, Equifax, one of the “big three” consumer credit reporting agencies, announced a massive data breach affecting 143 million U.S. consumers—almost half the population of the entire United States. By the time the dust had settled, the company announced that 146.6 million U.S. consumers were impacted, as well as approximately 15 million U.K. citizens and 19,000 Canadians.1
According to Equifax’s press release, “[T]he information accessed primarily includes names, Social Security numbers (SSNs), birth dates, addresses and, in some instances, driver’s license numbers. In addition, credit card numbers for approximately 209,000 U.S. consumers, and certain dispute documents with personal identifying information for approximately 182,000 U.S. consumers, were accessed.”2
Nearly half of all SSNs had been exposed in one fell swoop. “This is about as bad as it gets,” said Pamela Dixon, executive director of the World Privacy Forum. “If you have a credit report, chances are you may be in this breach. The chances are much better than 50 percent.”3
Equifax had quietly spent six weeks investigating its breach and had the luxury of planning its own disclosure. In preparation for the public announcement, it had:
Put together a polished press release.
Retained cybersecurity attorneys from the firm King & Spalding LLP.
Hired the forensics firm Mandiant to investigate.
Reported the incident to the FBI.
Set up a website, www.equifaxsecurity2017.com, which (in theory) allowed consumers to check whether they were affected and to register for the remedial package if so.
Set up call centers to assist consumers. According to Chief Executive Officer Rick Smith, this involved hiring and training thousands of customer service representatives in less than two weeks.
Developed a “robust package of remedial materials,” which, according to Smith, included “(1) monitoring of consumer credit files across all three bureaus, (2) access to Equifax credit files, (3) the ability to lock the Equifax credit file, (4) an insurance policy to cover out-of-pocket costs associated with identity theft, and (5) dark web scans for consumers’ social security numbers.”4
It looked good on paper—but it all went terribly wrong.
Immediately following the breach notification, Equifax’s stock prices took a nosedive. Shortly thereafter, the chief information officer (CIO) and chief security officer (CSO) resigned. Within a few weeks, CEO Rick Smith would resign as well (although he was later called to testify before Congress, where his statements fueled public outrage).
Within two months of the breach, Equifax was facing more than 240 consumer class-action lawsuits, as well as lawsuits filed by financial institutions and shareholders. The company reported in its quarterly SEC 10-Q filing that it was “cooperating with federal, state, city and foreign governmental agencies and officials investigating or otherwise seeking information and/or documents . . . including 50 state attorneys general offices, as well as the District of Columbia and Puerto Rico, the Federal Trade Commission (FTC), the Consumer Finance Protection Bureau (CFPB), the U.S. Securities and Exchange Commission (SEC), the New York Department of Financial Services, as well as other regulatory agencies in the United States, the United Kingdom, and Canada.5
By the time Equifax released its first-quarter report for 2018, the company had spent $242.7 million in response to the breach. In July 2019, Equifax agreed to pay up to $700 million as part of a settlement with the FTC, the CFPB, and 50 U.S. states and territories.
The breach shone a spotlight on the “underregulated” data brokerage industry. A flurry of new legislation was proposed in Congress, such as bills to support national data breach notification, credit report error correction, and even the “Freedom from Equifax Exploitation (FREE) Act,” which would give consumers more control over credit report freezes and fraud alerts. There was even a proposed “Data Broker Accountability and Transparency Act,” which would “press data broker companies, including recently breached credit report company Equifax, to implement better privacy and security practices.”6
“Equifax will not be defined by this incident, but rather, by how we respond,” said CEO Rick Smith valiantly, on the day the breach was announced. It was true. While the Equifax breach itself was bad, what turned it into an utter disaster was the company’s response, as we will see. In its immediate response to the breach, Equifax made choices that destroyed the public’s trust by undermining the perception of its competence, character, and caring. This led to a reckoning not just for Equifax but for the data brokerage industry as a whole.
3.1 Crisis and Opportunity
According to crisis management expert Steven Fink:7
A crisis is a fluid and dynamic state of affairs containing equal parts danger and opportunity. It is a turning point, for better or worse. The Chinese have a word for this: wei-fi.
As any experienced cybersecurity professional will tell you, most data breaches are “a fluid and dynamic state of affairs” (which is part of why is it so challenging to plan your response ahead of time). Every data breach (or suspected data breach) involves inherent danger. There is, of course, the obvious risk that a criminal will acquire and misuse sensitive information. There is the risk of outrage and loss of goodwill of customers, shareholders, and employees. There is the danger of lawsuits and fines. There is the risk of symbolic and unnecessary firings or reorganizations that damage morale and business operations. There is potential for direct financial, reputational, and operational damage.
And yet, data breaches can present enormous opportunities. When you are caught in the midst of a crisis, it can be hard to focus on the positive, but doing so can reap rewards. Data breaches happen for a reason (in fact, like car accidents, they are usually the result of multiple failures). In response to a data breach, we have seen organizations suddenly engage customers, employees, and shareholders more effectively than ever before, taking great pains to listen, understand, and react. Data breaches can quickly oust ineffective leaders and spur much-needed management changes. They can inspire management to appropriately prioritize and invest in modern computer technology, which increases both security and efficiency. They can be catalysts that propel organizations and even whole industries to become stronger in the long run: more secure, more organized, and more effective communicators.
The outcome of a crisis depends on how you react. Unfortunately, relatively few organizations plan for data breaches as a potential crisis, and therefore don’t have the necessary resources in place to effectively manage data breaches that escalate to this level. Much like organizations that handle hazardous waste, any organization that stores, processes, or transmits a significant volume of sensitive data should be prepared to handle a data breach crisis.
3.1.1 Incidents
Today, the majority of organizations that plan for data breaches include it as part of their cybersecurity incident response program, which is typically developed within the IT department. This is largely for historical reasons and not because it is the best strategy. In the early 2000s, virulent worms such as Blaster, Slammer, and MyDoom wreaked havoc across networks, infecting hundreds of thousands of computers and causing network outages. Information security teams prepared by implementing antivirus, network monitoring, intrusion detection, patching, and reimaging mechanisms. It was clear that the community needed a model for planning and responding to these types of threats.
In January 2004, the National Institute of Standards and Technology (NIST) released its first Computer Security Incident Handling Guide. What is an “incident”? According to NIST: “A computer security incident is a violation or imminent threat of violation of computer security policies, acceptable use policies, or standard security practices.”8
The classic NIST model breaks a cyclical incident response process into four high-level phases, shown in Figure 3-1:
Preparation
Detection and Analysis
Containment, Eradication, and Recovery
Post-Incident Activity
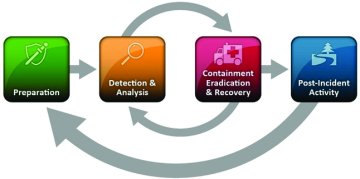
FIGURE 3-1 The NIST incident response lifecycle. Source: NIST, Computer Security Incident Handling Guide.
Theoretically, responders move through these phases of response in roughly linear cycle, returning to previous phases repeatedly as needed.
The NIST incident response lifecycle model actually worked very well when applied to the most widespread cybersecurity incidents of the early 2000s. When a virus or worm was detected, it was analyzed and then “contained” using network throttling or antivirus. The infected system was cleaned or reimaged (“eradication”); data was restored (“recovery”); and finally the incident was documented and (if necessary) discussed at a postmortem meeting.
Since then, organizations throughout the nation have used it as the basis for planning and managing cybersecurity incident response, including data breaches. And therein lies the problem: While the NIST guide is very helpful for managing many kinds of computer security incidents, as we will see, a data breach is typically not just an incident and therefore must be managed differently.
3.1.2 Data Breaches Are Different
Where in the NIST incident response lifecycle is the part where regulators fine your organization for negligence? Where does the CEO make a public statement? Where are the notification letters, the phone calls to insurers, the class-action lawsuits?
The NIST model can supposedly apply to “loss of data confidentiality,” but frankly, the tidy NIST model isn’t all that useful when managing a data breach. Most organizations include data breaches in cybersecurity incident response plans, but when an actual data breach occurs, the playbook goes out the window.
3.1.3 Recognizing Crises
Crisis management expert Ian Mitroff carefully differentiates between an incident and a crisis as follows:
An incident is “a disruption of a component, a unit, or a subsystem of a larger system, such as a valve or a system generator in a nuclear plant. The operation of the whole system is not threatened and the defective part is merely repaired.”
A crisis is “a disruption that . . . affects a system as a whole.”9
Steven Fink further defines a crisis as “any prodromal situation that runs the risk of”:
Escalating in intensity.
Falling under close media or government scrutiny.
Interfering with the normal operations of business.
Jeopardizing the positive public image presently enjoyed by a company or its officers.
Damaging a company’s bottom line in any way.10
Data breaches, by their very nature, create risks in all five of Fink’s categories above.
3.1.4 The Four Stages of a Crisis
The NIST incident response lifecycle is very useful for certain types of incidents. However, the purpose of having a model is to help us to better understand a situation and respond more effectively. When it comes to data breaches, Fink’s crisis management model is a more useful tool for understanding data breach management and response, as we will see throughout this book.
According to Fink, every crisis moves through four stages. These stages are:11
Prodromal - The “precrisis” phase, in which there are warnings or precursors that, if acted upon, can enable responders to minimize the impact of the crisis.
Acute - The “time when chaos reigns supreme,” according to Fink. At this stage, the crisis has become visible outside the organization, and leadership must address it.
Chronic - During this stage, “litigation occurs, media exposes are aired, internal investigations are launched, government oversight investigations commence.” As the name implies, the chronic stage can last for years.
Resolution - The crisis is settled and normal activities resume.
These stages apply neatly to data breaches, which typically do include a prodrome (such as an intrusion detection system alert), followed by an acute phase (such as an intense media scandal). This results in lawsuits, public outcry, internal investigations, etc., as described in the chronic phase. Finally, the breached organization may reach the resolution stage, typically after undergoing changes to processes and procedures. It can take years to get there.
The goal of crisis management is to “manage the prodrome so successfully that you go from prodrome to resolution without falling into the morass of the acute and chronic stages.”12 The same is true of data breaches: the best way to manage a data breach is to prevent it from occurring in the first place. If that is not possible, the next best technique is to rely upon a strong detection and response program, so that your response team can identify the earliest signs of an intrusion and react quickly enough to minimize the risk of data exposure. Effective network instrumentation, logging, and alerting are key elements of a strong detection and response program. Finally, if a data breach reaches the acute crisis phase, then it is important to have a strong crisis management and crisis communications program in place. This latter piece—crisis communications—is critical. It is not enough to manage the data breach crisis itself; you must also take care to manage the perception of the crisis.