- Impacts
- General Patterns in Insider Theft of Intellectual Property Crimes
- The Entitled Independent
- The Ambitious Leader
- Theft of IP inside the United States Involving Foreign Governments or Organizations
- Mitigation Strategies for All Theft of Intellectual Property Cases
- Mitigation Strategies: Final Thoughts
- Summary
Mitigation Strategies: Final Thoughts
We devoted a good deal of this chapter to technical countermeasures. Figure 3-9 depicts organizational issues of concern in the theft of intellectual property cases in our database. We addressed the technical issues in the previous section, but there are nontechnical issues worth noting as well. For instance, notice that the most prevalent issue of concern is an employee who went to work for a competitor. Therefore, you might want to monitor emails going to a competitor. We provide a control for doing that in Chapter 7, Technical Insider Threat Controls. Also, note the second most prevalent issue of concern: change in employment status, which would account for the insiders who stole information within 30 days of resignation. The third most prevalent issue is foreign national/non-U.S. native, which we covered in depth in the section Theft of IP inside the United States Involving Foreign Governments or Organizations earlier in this chapter. The fourth issue, employee/coworker susceptibility to recruitment, applies in all of the Ambitious Leader cases.
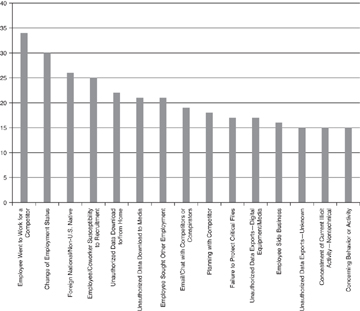
Figure 3-9 Issues of concern
One final thought regarding the 30-day window: You should review your access-termination procedures associated with employee and contractor exit procedures. Several cases provided evidence that insiders remotely accessed systems by using previously authorized accounts that were not disabled upon the employee’s exit. Precautions against this kind of incident seem to be common sense, but this trend continues to manifest in newly cataloged cases.
