- Impacts
- General Patterns in Insider Theft of Intellectual Property Crimes
- The Entitled Independent
- The Ambitious Leader
- Theft of IP inside the United States Involving Foreign Governments or Organizations
- Mitigation Strategies for All Theft of Intellectual Property Cases
- Mitigation Strategies: Final Thoughts
- Summary
The Entitled Independent
This section describes the model of the Entitled Independent, an insider acting primarily alone to steal information to take to a new job or to his own side business.
Based on our review of incident descriptions and interviews with victim organizations, investigators, and prosecutors of insider cases, we determined that most insiders felt entitled to take the information they were accused of stealing. The majority of the insiders stole information that they had worked on while employed by the organization.
Insider Contribution and Entitlement
Figure 3-3 shows how the insider’s feeling of entitlement toward the information he develops escalates over time. The employee comes into your organization with a desire to contribute to its efforts. As time goes on and he develops information, writes source code, or creates products, his contribution becomes more tangible. These insiders, unlike most employees and contractors, have personal predispositions that result in a perceived sense of ownership and entitlement to the information created by the entire group. The longer he works on the product, the more his sense of entitlement grows.
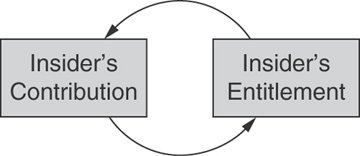
Figure 3-3 Insider entitlement
This sense of entitlement can be particularly strong if the insider perceives his role in the development of products as especially important. If his work is dedicated to a particular product—for example, development of a software system, or the building of customer contact lists—he may have a great sense of ownership of that product or information. This leads to an even greater sense of entitlement. In addition, consistent with good management practice, individuals may receive positive feedback for their efforts, which may further reinforce their sense of ownership, because of their predispositions.
Evidence of entitlement was extreme in a few cases. One Entitled Independent, who had stolen and marketed a copy of his employer’s critical software, created a lengthy manuscript detailing his innocence and declaring that everyone at the trial had lied. After being denied a raise, another insider stole the company’s client database and threatened to put them out of business on his way out the door.
What Can You Do?
Knowing that insiders who steal IP tend to steal the assets they helped to develop is a key factor in designing a mitigation strategy. If you can identify your critical intellectual property, you can narrow down the list of employees and contractors who are at highest risk of stealing it to those who are working on it now or have worked on it in the past.
In addition, keep in mind that people move around within your organization. How good are you at adjusting access controls as those moves happen? Just because someone has moved to another project or area of the organization doesn’t mean he doesn’t still feel a sense of entitlement to his past work. Erosion of access controls is a problem that needs to be solved in order to reduce risk of insider theft of intellectual property. Almost three-quarters of the insiders in our theft of IP cases had authorized access to the information stolen at the time of the theft, but that doesn’t mean that all of them should have had access. In many organizations, employees tend to transfer over time to different parts of the organization. They often accumulate privileges needed to perform new tasks as they move, without losing access they no longer need. Unfortunately, many insiders, at the time when they stole information, had accesses above and beyond what their job descriptions required.
We suggest that you periodically review and adjust your access controls for critical assets. We helped one organization set up an effective mechanism for controlling access once an employee transfers to another group. The organization realized that it couldn’t disable the employee’s access immediately upon transfer since there is typically a transition period in which the employee still needs access to his old team’s information. So the organization set up an automated email to be sent from its HR system to the employee’s previous supervisor three months after the date of transfer. This email lists all of the email aliases the employee is on, shared folders and collaboration sites to which the employee has access, and so on, and suggests that the supervisor contact IT to disable any access that is no longer necessary. This mechanism has been very successful in controlling the erosion of access controls in the organization.
Some insiders exhibited an unusual degree of possessiveness toward their work before stealing it. For instance, a few insiders kept all source code on their own laptops and refused to store it on the file servers, so they would have full control over it. This type of behavior should be recognized and remediated as early as possible.
Insider Dissatisfaction
Dissatisfaction played a role in many of the Entitled Independent cases. Dissatisfaction typically resulted from the denial of an insider’s request, as shown in Figure 3-4. Denial of an employee or contractor request can lead to dissatisfaction, which in turn decreases the person’s desire to contribute. This also affects the person’s sense of loyalty to you. Dissatisfaction often spurred the insider in our cases to look for another job; the majority had already accepted positions with another company or had started a competing company at the time of their theft. Once the insider receives a job offer and begins planning to go to a competing organization, his desire to steal information increases. This desire is amplified by his dissatisfaction with his current employer and his sense of entitlement to the products developed by his group.
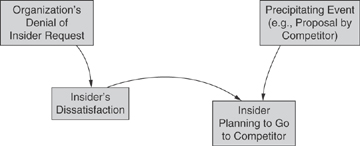
Figure 3-4 Insider dissatisfaction leading to compromise
In one-third of the cases, the insider actually used the proprietary information to get a new job or to benefit his new employer in some way.
In more than one-third of the cases, the insider took the information just in case he ever needed it, with no specific plans in mind. One insider actually broke into his organization’s systems after he was terminated to find out whether the organization had made any further progress on the product he had helped develop while he worked there.
What Can You Do?
It is inevitable that many of your employees will find new jobs at some point in time. Now that you understand that these departing employees could pose increased risk of insider theft of intellectual property, you should consider a review of your termination policies and processes. As soon as an employee turns in his resignation, you need to be prepared to act, as you will see in the next section. If you can quickly and easily identify the critical information that employee has access to, you can kick into prevention and detection mode.
Also, food for thought: Some of the insiders who stole IP were contractors. How do you handle contractors when they leave your organization? In our insider threat assessments we have discovered a disturbing trend in ill-defined or loosely enforced procedures for contractor terminations. Although contractors only account for 12% of our insider theft of IP crimes, the risk they pose should not be disregarded. Contract award cycles can range from five years, to three, to even one year. Are you able to track access granted to contractors and ensure appropriate access even when contractors and contracting organizations change on a frequent basis?
Insider Theft and Deception
As shown in Figure 3-5, eventually the desire to steal information becomes strong enough, leading to the theft and finally the opportunity for you to detect the theft. Perhaps someone observes an employee’s actions, or consequences of those actions, that seem suspicious in some way. The most likely person to discover an insider theft according to our data is a nontechnical employee; in cases where we were able to isolate the person who discovered the incident, 72% were detected by nontechnical employees. Therefore, you should have processes in place for employees to report suspicious behavior, employees should be aware of those processes, and you should follow up on reports quickly, particularly if they concern an employee who fits the profile described in our models.
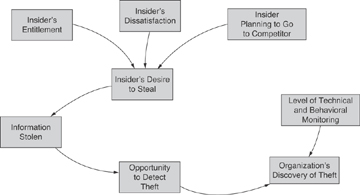
Figure 3-5 Insider theft and deception
Our Entitled Independents did not exhibit great concern with being caught. Even though signed IP agreements were in place in around 40% of the cases, fewer than one-quarter of the Entitled Independents tried to deceive the organization while taking their information. While explicit deception is not a major factor in most of these crimes, the fact that it did occur in one-fourth of them suggests that you need to anticipate it when designing your countermeasures.
For example, upon announcing his resignation, one insider lied to his manager and said he had no follow-on employment, even though he had told a coworker about his new job at a competitor. If you become aware of deliberate deception like this, it may be an indicator of problems to come. Deceptions generally make it harder for you to sense the risk of theft, and that is why the insider does it. But if you are vigilant, deceptions may be discovered, alerting you to increased risk of insider threat. If the organization in this example had known that the insider had given contradictory information to his manager and coworker, it may have been forewarned of the heightened risk.
In general, your accurate understanding of your risk is directly related to your ability to detect the insider’s illicit actions. With sufficient levels of technical and behavioral monitoring, these actions may be discoverable.
Most of these crimes tend to be quick thefts around resignation. More than one-half of the Entitled Independents stole information within one month of resignation, which gives you a well-defined window of opportunity for discovering the theft prior to employee termination. It is important that you fully understand the one-month window, however, as it is a bit more complex than it first appears. First, the one-month window includes the month before the insider turns in his resignation and the month after he resigns; actually two months total. This means that you need to have technical measures in place at all times so that you can go back in time and review past online activity. Second, some of these insiders stole IP long before resignation; just because they stole it within one month of resignation doesn’t mean that is when they first started stealing it. Some of them stole slowly over time, committing their final theft right before resignation. However, fewer than one-third of the insiders continued their theft for more than one month.
One insider planned with a competing organization abroad and transferred documents to the company for almost two years prior to her resignation. However, for the most part, the insiders did steal the information quickly upon resignation.
In one case the insider accepted a position with a competing organization, resigned his position, and proceeded to download proprietary information to take with him to the new company before his last day of work. He stole the information despite warnings by his new employer not to bring any proprietary information with him to his new position. When questioned about the theft, the insider admitted to downloading the information, saying that he hoped to use it if he ever started his own business.
In a similar case, the insider accepted a position with a competitor and started downloading documents containing trade secrets the very next day. A few weeks later, after several sessions of high-volume downloading, the insider left the organization and started working for the competitor. Just two days after starting his new job, the insider loaded the stolen files onto his newly assigned laptop, and within a month had emailed the trade secrets to his new coworkers. This exemplifies the lack of any effort to conceal the theft.
A wide variety of technical means were used in the theft cases to transfer information, including email, phone, fax, downloading to or from home over the Internet, malicious code collection and transmission, and printing out material on the organizations’ printers. One particularly vengeful insider acted in anger when his employer rewarded executives with exorbitant bonuses while lower-level employees were receiving meager raises or being laid off. He began downloading confidential corporate documents to his home computer, carrying physical copies out of the offices, and emailing them to two competitors. Neither of the two competitors wanted the confidential information and both sent the information they received back to the victim organization. This insider also made no attempt to conceal or deny his illicit activity.
We will explore the technical details of the theft of IP cases later in this chapter, following the Ambitious Leader model.
What Can You Do?
Our case data suggests that monitoring of online actions, particularly downloads within one month before and after resignation, could be particularly beneficial for preventing or detecting the theft of proprietary information. You need to consider the wide variety of ways that information is stolen and design your detection strategy accordingly. Data leakage tools12 may help with this task. Many tools are available that enable you to perform functions such as the following:
- Alerting administrators to emails with unusually large attachments
- Tagging documents that should not be permitted to leave the network
- Tracking or preventing printing, copying, or downloading of certain information, such as PII or documents containing certain words such as new-product codenames
- Tracking of all documents copied to removable media
- Preventing or detecting emails to competitors, to governments and organizations outside the United States, to Gmail or Hotmail accounts, and so on
You might also consider a simple mechanism to protect yourself from being the unknowing recipient of stolen IP from another organization. As part of your IP agreement that you make new employees sign, you might want to include a statement attesting to the fact that they have not brought any IP from any previous employer with them to your organization. We are heartened by the fact that many of the theft of IP cases in our database were detected by the new employer, and reported to the victim organization and/or law enforcement. You should be sure that you have a process defined for how you would respond to that twist of insider threat. In addition, you may consider asking departing employees to sign a new IP agreement, reminding them of the contents of the IP agreement while they are walking out the door.
