Understanding the Support Center
The purpose of an IT support center is to provide technical support to users. This includes starting (or booting) a computer, logging on, configuring a computer, configuring and running applications, and accessing network resources. The support center might support users within the same organization or, in other cases, the support center might support external customers of the organization.
For example, large organizations have in-house IT departments to assist users within the organization. Help desk employees working in a support center division of the IT department assist other employees in the same organization. In contrast, Internet service providers (ISPs) provide Internet access to their subscribers and employ help desk personnel to assist ISP subscribers. Customers that are having problems accessing the Internet or using any of the ISP services contact the support center for assistance.
A Little History
Prior to the 1970s, computers used within an organization were restricted to mainframes that typically took up a full room. Many were the size of a large refrigerator and had only a fraction of the computing ability of today’s computers. Organizations lucky enough to have these computers employed a few highly qualified personnel to maintain and operate them.
In 1976, Steve Jobs and Steve Wozniak started Apple and began selling the first computer for home use, the Apple I. In 1981, IBM created the IBM Personal Computer (or IBM PC), which became a standard used in many organizations by regular employees. IBM contracted with a small start-up company called Microsoft, founded by Bill Gates and Paul Allen, to provide the disk operating system (DOS) for the IBM PC. Back then, Bill Gates had a vision of “a computer on every desk and in every home” and used this DOS as a starting point.
The DOS used on IBM PCs included a disk operating system called PC-DOS. However, Microsoft retained the rights to the software and began selling it as MS-DOS (Microsoft Disk Operating System). Several other manufacturers began creating their own PCs running MS-DOS, and these PCs provided much of the same functionality as IBM PCs. These IBM PC-compatible computers came to be known as clones, and in time, the clones overtook IBM’s market share. IBM no longer manufactures PCs, but the combination of these events helped the PC market expand exponentially.
Today’s world is much closer to Bill Gates’s vision of a computer on every desk and in every home. Moreover, it is very common for almost every employee within many organizations to have a PC. Over time, Microsoft developed increasingly more sophisticated Windows operating systems and applications. Additionally, many other companies developed highly useful applications that streamlined work processes, steadily increasing overall employee productivity.
In 1969, the Advanced Research Projects Agency Network (ARPANET) started developing a network used by universities and research laboratories in the United States to share information between each other over long distances. This morphed into the Internet in the 1980s, and eventually became a network accessible by users around the world. Currently, it’s estimated that more than 2 billion users have access to the Internet.
Along with the explosion of the Internet, organizations began connecting computers and other resources together in local area networks (LANs). Large organizations with multiple buildings spread across a campus connected the building LANs together in metropolitan area networks (MANs). Organizations with buildings or campuses in multiple locations connected their LANs together in wide area networks (WANs).
Note that in the span of just a couple of decades (from the ‘70s to the ‘90s), computer usage within organizations sharply increased. Previously, organizations used very few computers and needed very few IT support personnel. However, as the IT usage grew, there became an obvious need for more IT support personnel.
The Evolution of the Support Center
While the growth of computer use, networks, and the Internet has provided significant benefits for organizations, these computers, applications, and networks have become increasingly complex. Ideally, they work as expected all the time. In reality, computers and networks display a wide range of problems from minor operability problems to complete failure. Users cannot be expected to know all the technical details required to maintain and troubleshoot computers and networks any more than they can be expected to know everything about phones and all the details about the plain old telephone system (POTS) or the more sophisticated Integrated Services Digital Network (ISDN). Instead, organizations realized that they needed specialists within an IT support center to maintain the computers and networks, and help the users when necessary.
The support center role has evolved over time. When an organization had only a few desktop computers, the support center was typically one or two computer experts. These experts did everything related to the computers. As computer use grew, it was apparent this model was no longer effective. Instead, organizations began to separate the roles of the IT personnel based on different needs.
It’s important to understand that the help desk is a cost center instead of a profit center. A profit center generates revenue for a company and includes departments such as sales and marketing. These departments generate sales and help earn profits for the company. A cost center generates additional costs for a company without bringing in any direct revenue. For example, the IT department does not generate any sales, so it does not bring in any additional revenue. Instead, it only generates costs for IT hardware, software, and services.
Companies that care about the bottom line focus on increasing revenue and decreasing costs, so the idea of creating or expanding a help desk isn’t always embraced. However, over time, many organizations realize that providing IT support to users significantly improves their overall productivity—but the value of the help desk still needs to be justified. One way costs are justified is through metrics discussed in the Typical Incident Process section later in this chapter.
Understanding an Incident and Incident Management
When talking about a help desk and its functions, it’s important to understand two key terms: incident and incident management. In simple terms, you can think of an incident as a problem. Customers typically report the problem to the help desk and the help desk technicians take steps to resolve it. An organization implements incident management processes to ensure that all incidents are resolved to the best ability of the organization.
However, there are definitions that are more specific. Chapter 9, “Business Skills,” includes information on the Information Technology Infrastructure Library (ITIL). ITIL is a group of books written and published by the United Kingdom’s Office of Government and Commerce (OGC). It has been around since the 1980s and has improved and matured since then. ITIL provides organizations with a collection of good practice concepts that can improve IT processes within any IT organization. Its goal is to help organizations identify functions, roles, and processes that can benefit from these concepts to ensure IT services remain available on a consistent basis.
ITIL provides the following paraphrased definitions for an incident and incident management:
- Incident. An incident is an unplanned interruption or a reduction in the quality of an IT service. It can also be the failure of a fault tolerant or redundant solution designed to increase the availability of a service. For example, the failure of one disk in a mirror set is an incident.
- Incident Management. This includes all processes and procedures used to deal with incidents. Incidents might be reported by users, by technical staff, or from automated tools that perform event monitoring and reporting.
The Role of the Support Center
Organizations often divide an IT department into several different divisions. Personnel working within these divisions are able to focus on specific IT requirements and become experts within that area. While the following list is not inclusive, it does identify many of the common divisions:
- Help Desk
- Infrastructure
- Servers
- Security
- Software
Help Desk
The help desk provides direct support to the end users. Support provided by the help desk varies between organizations; later in this chapter, the section “Services Provided to Users” explains many of the common services organizations choose to provide. Overall, this book focuses on the help desk division, or the help desk function, within an IT department.
Infrastructure
Large networks have dedicated technicians and administrators to maintain the network infrastructure. This includes network connections and hardware such as routers and switches, and access to other networks such as the Internet. If an organization doesn’t have a dedicated security team, technicians maintaining the network would also maintain firewalls and proxy servers that are connected to the Internet. In some smaller organizations, infrastructure technicians are part of another division, such as the servers division.
Servers
Organizations typically have one or more servers that require some advanced knowledge to configure and maintain. Some examples are file servers where users store and access files, mail servers used for email, and web servers used to host web sites. Administrators that maintain these servers might also work on the network infrastructure.
Security
Security has become increasingly important to organizations due to the frequency of attacks and the high level of threats. Criminals often attack networks trying to steal data such as customer information or company secrets. In other cases, criminals launch sophisticated denial of service (DoS) attacks with the goal of taking down a server, network, or any type of service provided by the company.
Malicious software (malware) includes viruses, worms, Trojans, logic bombs, and more. Antivirus software helps protect against malware but it is only useful when all appropriate systems have antivirus software installed, and it is kept up-to-date. Years ago, organizations depended on employees to maintain and update antivirus software, but this rarely worked. Today, security experts deploy, update, and maintain this software remotely.
Network security experts maintain firewalls and Internet-facing servers to provide a level of protection for the internal network. In many cases, these network security experts also manage the antivirus software for the company. Proactive organizations task these security experts with performing vulnerability assessments and risk analysis. Even if an organization doesn’t have a dedicated team of security professionals, technicians in other areas of the company will still be responsible for maintaining IT security.
Software
Some organizations develop their own software. They have dedicated programmers to create, maintain, and troubleshoot these applications. Programmers rarely work on regular servers or the network infrastructure, though they might be responsible for the configuration and maintenance of web servers and database servers.
An effective IT department has a team mentality and recognizes the need for the different divisions to work together. Even though the separate divisions have different responsibilities, they frequently interact with other.
IT Tiers within an Organization
Organizations typically organize support to their customers in separate levels, or tiers. Most organizations that use tiers have three internal tiers, and some identify a fourth external tier. Technicians at lower-level tiers try to resolve the problem to the best of their ability. If they are unable to resolve the problem, they escalate the problem. In other words, they pass the problem on to a technician at a higher tier to resolve the problem.
Support personnel at each tier might work on the same incident or trouble call. For example, when the customer makes initial contact with a tier 1 technician, this technician logs it as an incident and begins working on it. If the tier 1 technician cannot resolve the incident, this technician escalates the incident to a higher tier. As the incident escalates through the tiers, technicians at each level review past activity and log their actions. This ensures that all technicians are able to see the full scope of the problem and the previous actions taken to resolve it.
Figure 1-1 shows an overview of the tiers, and the following bullets describe them in more depth.
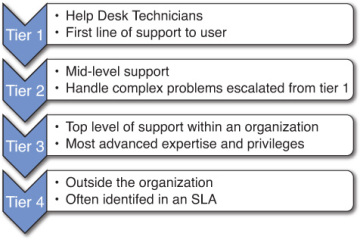
FIGURE 1-1 Four tiers of support within an organization.
- Tier 1. Help desk personnel are tier 1 and provide basic support to users. Technicians have basic skills, knowledge, and privileges to resolve simple and common problems.
- Tier 2. Technicians with a higher level of knowledge, experience, and permissions work at tier 2 and can assist tier 1 technicians resolve more complex problems. These technicians often have experience at the tier 1 level, or at least have experience providing direct assistance to users. In most cases, these technicians have dedicated jobs in other areas of the IT department, such as maintaining servers or the network infrastructure.
- Tier 3. The highest tier in most organizations is tier 3. Administrators and technicians at this tier troubleshoot and resolve the most difficult or complex problems. Just as tier 2 technicians have other job responsibilities, tier 3 technicians also have other responsibilities. For example, they might be working on IT projects related to expanding IT services or migrating older systems and data to newer systems.
- Tier 4. Many organizations have service level agreements (SLAs) with outside organizations. An SLA stipulates the performance expectations and identifies support services provided by the vendor. When certain problems appear, they contact the outside entity to resolve them. For example, an organization could have an SLA with Microsoft and work with Microsoft personnel to resolve problems related to Microsoft operating systems and software. Similarly, they might have an SLA with Dell to replace failed hardware.
While tier 1 technicians will try to handle most problems without escalating them, there are situations when they quickly escalate an incident. For example, if technicians realize that the same incident is affecting multiple users, they will escalate the incident to a higher tier. Many times, help desk supervisors make the call to escalate an incident and then communicate updates to help desk personnel to ensure they don’t work on an escalated problem.
