- Introduction
- Principle 1: There Is No Such Thing As Absolute Security
- Principle 2: The Three Security Goals Are Confidentiality, Integrity, and Availability
- Principle 3: Defense in Depth as Strategy
- Principle 4: When Left on Their Own, People Tend to Make the Worst Security Decisions
- Principle 5: Computer Security Depends on Two Types of Requirements: Functional and Assurance
- Principle 6: Security Through Obscurity Is Not an Answer
- Principle 7: Security = Risk Management
- Principle 8: The Three Types of Security Controls Are Preventative, Detective, and Responsive
- Principle 9: Complexity Is the Enemy of Security
- Principle 10: Fear, Uncertainty, and Doubt Do Not Work in Selling Security
- Principle 11: People, Process, and Technology Are All Needed to Adequately Secure a System or Facility
- Principle 12: Open Disclosure of Vulnerabilities Is Good for Security!
- Summary
- Test Your Skills
Principle 11: People, Process, and Technology Are All Needed to Adequately Secure a System or Facility
As described in Principle 3, “Defense in Depth as Strategy,” the information security practitioner needs a series of countermeasures and controls to implement an effective security system. One such control might be dual control, a practice borrowed from the military. The U.S. Department of Defense uses a dual control protocol to secure the nation’s nuclear arsenal. This means that at least two on-site people must agree to launch a nuclear weapon. If one person were in control, he or she could make an error in judgment or act maliciously for whatever reason. But with dual control, one person acts as a countermeasure to the other: Chances are less likely that both people will make an error in judgment or act maliciously. Likewise, no one person in an organization should have the ability to control or close down a security activity. This is commonly referred to as separation of duties.
Process controls are implemented to ensure that different people can perform the same operations exactly in the same way each time. Processes are documented as procedures on how to carry out an activity related to security. The process of configuring a server operating system for secure operations is documented as one or more procedures that security administrators use and can be verified as done correctly.
Just as the information security professional might establish process controls to make sure that a single person cannot gain complete control over a system, you should never place all your faith in technology. Technology can fail, and without people to notice and fix technical problems, computer systems would stall permanently. An example of this type of waste is installing an expensive firewall system (a network perimeter security device that blocks traffic) and then turning around and opening all the ports that are intended to block certain traffic from entering the network.
People, process, and technology controls are essential elements of several areas of practice in information technology (IT) security, including operations security, applications development security, physical security, and cryptography. These three pillars of security are often depicted as a three-legged stool (see Figure 2.3).
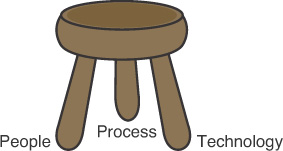
FIGURE 2.3 The people, process, and technology triad.
