- Licensed Features on ASA
- Managing Licenses with Activation Keys
- Combined Licenses in Failover and Clustering
- Shared Premium VPN Licensing
- Summary
Shared Premium VPN Licensing
It may become cost prohibitive to obtain multiple separate AnyConnect Premium Peers licenses if you manage a large number of Cisco ASA appliances that terminate SSL VPN, Clientless SSL VPN, and IPsec IKEv1-based remote-access VPN sessions. Even though individual appliances may reach the maximum expected number of concurrent VPN sessions at different times, it is unlikely that all of them will always remain at the peak load. Instead of obtaining a tiered AnyConnect Premium Peers capacity license to cover the worst-case scenario for each Cisco ASA in your network, you have the option of configuring your devices to share a pool of such licenses and request premium VPN session capacities as needed.
Shared Server and Participants
To utilize a shared license pool for AnyConnect Premium sessions, you need to designate one Cisco ASA in the network as the shared licensing server. Other ASA devices that terminate AnyConnect Premium sessions become shared licensing participants. The server maintains the shared licenses and issues them to participants as necessary. You can optionally designate one participant ASA as the backup shared licensing server; this device will manage the shared pool only when the primary shared server becomes unavailable.
Shared License
Like other licensed capabilities, the Shared License feature can be either enabled or disabled. However, it could also link with the tiered capacity of Shared AnyConnect Premium Peers when enabled. When the output of the show version or show activation-key command simply shows the Shared License feature as enabled, it means that the particular Cisco ASA can act as a shared licensing participant or a backup server. The same output from a shared licensing server also displays the associated quantity of shared licenses in the pool, as shown in Example 3-9.
Example 3-9 Shared Server License
Shared License : Enabled 56 days Shared AnyConnect Premium Peers : 1000 perpetual
Keep in mind that the Shared AnyConnect Premium Peers license is not available separately from the Shared License feature; the particular activation key must enable this capability and specify the shared session capacity in order to enable a shared licensing server. You cannot use the regular AnyConnect Premium Peers license to provision or expand the shared session pool. Only the participant license can activate with a time-based activation key; the shared server license must use the permanent key.
Shared Licensing Operation
After you install the appropriate licenses on the server and participants, you can configure these devices to share the licensed pool of AnyConnect Premium sessions. The server may also act as a participant without a separate license; it always uses the Shared AnyConnect Premium Peers capacity when terminating SSL VPN connections itself even if it has a regular AnyConnect Premium Peers license installed. Keep in mind that any Cisco ASA device may participate in a shared licensing domain under the following conditions:
- Each device has the Shared License feature enabled. Because hardware models do not have to match within a single domain, any device except a Cisco ASA 5505 can be the server or a participant.
- You configure each participant ASA with the same shared secret value as the licensing server.
- Each participant ASA has bidirectional IP reachability with the configured shared server and backup server, if applicable. The communication channel uses SSL encryption and allows crossing intermediate routers.
Each participant ASA follows this process when handling AnyConnect Premium connections:
- Register with the shared licensing server, report the hardware model and local license information, and continue periodic polling over the communication channel.
- Only when the system exhausts the local licensed capacity for AnyConnect Premium sessions, request additional session licenses from the shared pool in blocks of 50. The total count of locally licensed and shared sessions cannot exceed the Total VPN Sessions capacity for the platform. The server may not always provision the requested number of licenses if the remaining shared pool capacity is low.
- Send to the server periodic refresh messages indicating that the requested allocation is still active. If the server does not hear from the participant within three consecutive refresh intervals, the allocation may expire. However, the participant continues using the allocated shared session count for up to 24 hours. If the communication channel with the server remains severed after this grace period, the device falls back to using the local licensed capacity; only new connections are affected. Even if the communication channel re-establishes within the 24-hour period, the same shared pool capacity may no longer be available on the server.
- When the session count drops below the level that requires additional shared licenses, the client releases the allocated pool back to the server.
When you configure one of the participants to act as a backup shared licensing server, this unit must establish a communication channel to synchronize the pool information with the primary server first. When the primary licensing server goes down, the backup fully takes over the shared pool for up to 30 days of independent operation; the primary server resumes its normal duties after it comes back up. Upon initial synchronization, the backup server is only capable of five days of independent operation when the primary server goes offline; this period extends by one day every day up to the maximum of 30 days as long as the communication channel with the primary server remains operational. The following system log message is generated by the backup licensing server when the maximum allowed interval of independent operation is about to expire:
%ASA-4-444110: Shared license server backup has 15 days remaining as active license server.
Keep in mind that both peers in a failover pair have the exact same shared licensing role. In other words, you cannot configure the primary Cisco ASA as the shared licensing server and the secondary ASA as its backup. The secondary unit takes over as the primary licensing server after a failover event; you should configure some other ASA as the backup licensing server, if desired.
Configuring Shared Licensing
You should have the following information ready before starting the configuration process of Shared Licensing:
- Shared secret key that the given shared licensing group will use.
- Identity of the designated primary shared licensing server and its IP addresses on every interface that will accept connections from participants.
- If applicable, the IP address and the serial number of the Cisco ASA that will act as the backup shared licensing server; if this device participates in failover, you need the serial number of the secondary unit as well.
Licensing Server
Configure the primary licensing server through Cisco Adaptive Security Device Manager (ASDM) by navigating to Configuration > Device Management > Licensing > Shared SSL VPN Licenses. Figure 3-1 shows what the configuration panel looks like if the device has the appropriate license to act as the primary licensing server.
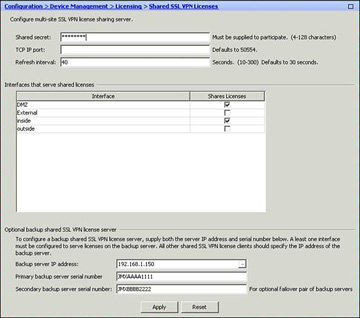
Figure 3-1 Shared Premium VPN Licensing ASDM Configuration Pane
Follow these steps to configure the shared licensing server on this ASDM panel:
- Set the shared secret. Configure the same value on all of the participants within the same shared licensing domain.
- Optionally, set a particular TCP port that the participants would use to connect to the server. It is not recommended to change the default value of 50554.
- Optionally, change the refresh interval that the participants use to regularly confirm the active status of a shared session count allocation. The server releases the allocation back into the shared pool if it does not hear from the participant for three times the configured refresh interval.
- Enable participant connections on the respective local interfaces of the shared server. Keep in mind that a participant can only connect to the “closest” interface of the licensing server. If the server ASA can reach a particular participant on the DMZ interface, that participant cannot connect to the server’s inside interface instead.
- Optionally, configure the IP address and the serial number of the Cisco ASA that will act as the backup shared licensing server. If this device has failover configuration, you need to specify the serial number of the failover peer as well.
Participants
After you have configured the shared licensing server, configure each participant using the following steps:
Specify the address of the closest interface of the shared licensing server and the shared secret value with the license-server command. If you changed the default TCP port on the server, you need to specify it here as well. The command has the following syntax:
license-server address server-IP secret shared-secret [port tcp-port]
If applicable, specify the IP address of the backup shared licensing server:
license-server backup backup-server-IP
Backup Licensing Server
To configure a participant to act as the backup licensing server, add the following command for each interface that would accept connections from other participants when the primary server is down:
license-server backup enable local-interface-name
Monitoring Shared Licensing Operation
Use the show shared license command to monitor the communication between the shared license server and its participants. This command also displays information about the shared pool size and utilization as well as the local platform limits. The specific output depends on whether you are looking at the server or a participant. Example 3-10 illustrates a sample output from a shared licensing server.
Example 3-10 Shared License Server Statistics
asa# show shared license
Shared license utilization:
AnyConnect Premium:
Total for network : 4500
Available : 4500
Utilized : 0
This device:
Platform limit : 750
Current usage : 0
High usage : 0
Client ID Usage Hostname
FCH12345678 0 ASA-5555
