- Impacts
- General Patterns in Insider Theft of Intellectual Property Crimes
- The Entitled Independent
- The Ambitious Leader
- Theft of IP inside the United States Involving Foreign Governments or Organizations
- Mitigation Strategies for All Theft of Intellectual Property Cases
- Mitigation Strategies: Final Thoughts
- Summary
The Ambitious Leader
This section describes the Ambitious Leader model. These cases involve a leader who recruits insiders to steal information with him—essentially a “spy ring.” Unlike the Entitled Independent, these insiders don’t only want the assets they created or have access to, they want more: an entire product line or an entire software system. They don’t have the access to steal all that they want themselves, so they recruit others into their scheme to help.
We omitted the What Can You Do? section from most of the Ambitious Leader scenarios because it is so similar to the Entitled Independent model. But we provide extensive advice at the end of the chapter when we explore the technical details in all of the cases.
More than half of the Ambitious Leaders planned to develop a competing product or use the information to attract clients away from the victim organization. Others (38%) worked with a new employer that was a competitor. Only 10% actually sold the information to a competing organization.
About one-third of our theft of IP cases were for the benefit of a foreign government or organization. The average financial impact for these cases was more than four times that of domestic IP theft. In these cases, loyalty to the insider’s native country trumped loyalty to the employer. Insiders with an affinity toward a foreign country were motivated by the goal of bringing value to, and sometimes eventually relocating in, that country.
In general, the cases involving a foreign government or organization fit the Ambitious Leader model. However, because the consequences of these crimes are much more severe, and both government and private organizations are so concerned about this threat, we have included a separate section at the end of the Ambitious Leader model that analyzes those crimes in a bit more depth.
The rest of this section describes additional aspects of the Ambitious Leader model not exhibited by Entitled Independents. These cases are more complex than the Entitled Independent cases, involving more intricate planning, deceptive attempts to gain increased access, and recruitment of other employees into the leader’s scheme.
The motivation for the Ambitious Leader is slightly different from that of the Entitled Independent. There was little evidence of employee dissatisfaction in the Ambitious Leaders. Insiders in this scenario were motivated not by dissatisfaction, but rather by an Ambitious Leader promising them greater rewards.
In one case, the head of the public finance department of a securities firm organized his employees to collect documents to take to a competitor. Over one weekend he then sent a resignation letter for himself and each recruit to the head of the sales department. The entire group of employees started work with the competitor the following week.
In another case, an outsider who was operating a fictitious company recruited an employee looking for a new job to send him reams of his current employer’s proprietary information by email, postal service, and a commercial carrier.
Except for the dissatisfaction of the Entitled Independent, the initial patterns for Ambitious Leaders are very similar. In fact, the beginning of the Ambitious Leader model is merely the Entitled Independent model without the “organization denial of insider request” and “insider dissatisfaction.” Most Ambitious Leaders stole the information that they worked on, just like the Entitled Independents. The difference is that they were not content only to steal the information they had access to; they wanted the entire system, program, or product line, and needed a more complex scheme to get it.
Theft took place even though IP agreements were in place for almost half (48%) of the Ambitious Leader cases. In at least one case, the insider lied when specifically asked if he had returned all proprietary information and software to the company as stipulated in the IP agreement he had signed. He later used the stolen software to develop and market a competing product in a foreign country.
Insider Planning of Theft
The Ambitious Leader cases involved a significantly greater amount of planning than the Entitled Independent cases, particularly the recruitment of other insiders. Other forms of planning involved creating a new business in almost half of the cases, coordinating with a competing organization in almost half of the cases, and collecting information in advance of the theft.
This aspect of the insider behavior is reflected in Figure 3-6, which describes the Ambitious Leader formulating plans to steal the information prior to the actual theft. This extensive planning is an additional potential point of exposure of the impending theft, and therefore results in measures by the insider to hide his actions. In most of the Ambitious Leader cases, the insider was planning the theft a month or more before his departure from the organization.
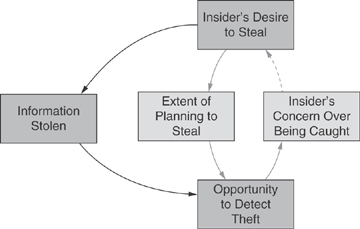
Figure 3-6 Theft planning by Ambitious Leader
The one-month window surrounding resignation holds for most Ambitious Leaders just as it does for Entitled Independents.
Increasing Access
In more than half of the Ambitious Leader cases, the lead insider had authorization for only part of the information targeted and had to take steps to gain additional access. In one case involving the transfer of proprietary documents to a foreign company, the lead insider asked her supervisor to assign her to a special project that would increase her access to highly sensitive information. She did this just weeks prior to leaving the country with a company laptop and numerous company documents, both physical and electronic.
As shown in Figure 3-7, the recruitment of additional insiders is the primary means Ambitious Leaders use to gain access to more information. The need for recruitment increases the amount of planning activity necessary to coordinate insider activities.
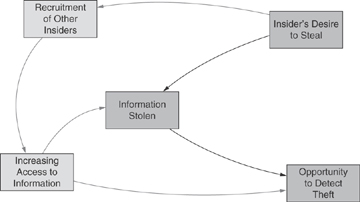
Figure 3-7 Increasing access by the Ambitious Leader
Organization’s Discovery of Theft
There are many more avenues for you to detect heightened risk of insider theft of IP in Ambitious Leader cases than in Entitled Independent cases. Entitled Independents are often fully authorized to access the information they steal, and do so very close to resignation with very little planning. In addition, Entitled Independents rarely act as if what they are doing is wrong, probably because they feel a proprietary attachment to the information or product. Ambitious Leaders, on the other hand, often have to gain access to information for which they are not authorized. This involves, in part, coordinating the activities of other insiders and committing deception to cover up the extensive planning required.
What Can You Do?
Figure 3-8 illustrates the avenues available for you to continually assess the risk you face regarding theft of IP. Because deception is such a prominent factor in Ambitious Leader cases, its discovery may be a better means to detect heightened insider risk here than in Entitled Independent cases.
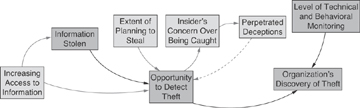
Figure 3-8 Organization’s discovery of theft of IP in Ambitious Leader cases
In some of the cases we reviewed, the organization only found out about the theft when the insider took his competing product to market or solicited business from his previous employer’s customers. While this detection is later than one would prefer, it is still not too late to take action and prevent further losses. However, we strongly suggest that you consider the countermeasures at the end of this chapter to facilitate earlier detection. Many of the incidents in our database were detected by nontechnical means, such as the following:
- Notification by a customer or other informant
- Detection by law enforcement investigating the reports of the theft
- By victims
- Reporting of suspicious activity by coworkers
- Sudden emergence of new competing organizations
You can use technical monitoring systems to detect insider theft of IP. More than one-half of the Entitled Independents and almost two-thirds of the Ambitious Leaders stole information within one month of resignation. Many of these involved large downloads of information outside the patterns of normal behavior by those employees. In more than one-quarter of the Ambitious Leader cases, an insider emailed or otherwise electronically transmitted information or plans from an organizational computer.
Keeping track of backups of critical information is also important—in one case an insider took the backup media from his computer on his last day of work. Understanding the potential relevance of these types of precursors provides a window of opportunity for you to detect theft prior to employee termination.
Of course, the earlier you can become aware of illicit plans the better. Early awareness depends on behavioral as well as technical monitoring and is more likely to catch incidents involving Ambitious Leaders than Entitled Independents. In Ambitious Leader scenarios, you need to look for evolving plans and collusion by insiders to steal information, including attempts to gain access to information over and above that for which an employee is authorized. There were behavioral or technical precursors to the crime in all of the Ambitious Leader cases.
One insider, over a period of several years, exhibited suspicious patterns of foreign travel and remote access to organizational systems while claiming medical sick leave. It is not always this blatant, but signs are often observable if you are vigilant.
