- Impacts
- General Patterns in Insider Theft of Intellectual Property Crimes
- The Entitled Independent
- The Ambitious Leader
- Theft of IP inside the United States Involving Foreign Governments or Organizations
- Mitigation Strategies for All Theft of Intellectual Property Cases
- Mitigation Strategies: Final Thoughts
- Summary
General Patterns in Insider Theft of Intellectual Property Crimes
The intent of our MERIT model of insider theft of intellectual property is to describe the general profile of insider theft of IP crimes. The MERIT models describe the patterns in the crimes as they evolve over time—profiling the life cycle of the crime, rather than profiling only the perpetrator.
The MERIT model of insider theft of IP was first published in 2009. The model was created using system dynamics modeling, which is described in the original report and in Appendix F, System Dynamics Background. Over the years, however, we have found that a higher-level view of that model is more useful in describing the patterns to practitioners so that clear, actionable guidance can be provided for mitigating these incidents. That higher-level form of the model and accompanying countermeasure guidance is presented in the remainder of this chapter.
As mentioned earlier, our overall model for theft of IP actually consists of two models: the Entitled Independent and the Ambitious Leader; we will present those one at a time. We have broken each model down into small pieces in this chapter in order to make it more understandable. The full model of the Entitled Independent is shown in Figure 3-1. Figure 3-2 shows the full model of the Ambitious Leader.
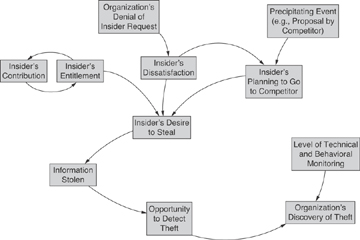
Figure 3-1 MERIT model of insider theft of IP: Entitled Independent
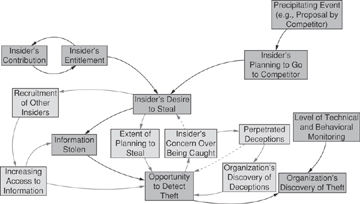
Figure 3-2 MERIT model of insider theft of IP: Ambitious Leader
