Top Cybersecurity Threats of 2020
World-renowned cybersecurity expert Sherri Davidoff shares the latest techniques hackers are employing for the top cybersecurity threats in 2020, along with tips for protecting your organization.
A new year brings new threats! Discover the top cybersecurity threats companies will face in 2020, based on the latest cases and trends observed by data breach experts. This year, watch out for:
- Cloud hacking
- Ransomware combined with exposure
- Sophisticated supply-chain exploitation
1. Cloud Hacking
Hackers are targeting the cloud and hybrid environments, leveraging increasingly sophisticated techniques. New cloud hacking toolkits have emerged which enable criminals to easily exploit common vulnerabilities. Common cloud hacking techniques include:
- Shared Architecture Flaws: Attackers take advantage of common cloud configuration flaws, such as the AWS metadata instance leveraged in the CapitalOne data breach.
- Cross-Tenant Attacks: Attackers comprise a virtual server and move laterally to access other resources, leveraging trusted access within the tenant.
- File Synchronization Poisoning: Attackers take advantage of file replication between the cloud and endpoints, using it to spread ransomware or malware throughout multiple cloud applications and hybrid environments.
- Credential Stuffing: Criminals leverage massive databases of stolen usernames and passwords and use them to attempt to login to other services. Credential stuffing rose to prominence in 2019, and experts anticipate that it will remain a top hacking technique in 2020.
- Cloud Orchestration Attacks: Organizations build workflows to automate and scale cloud-based services. By targeting a weak point in the workflow, attackers can establish a foothold and spread throughout the architecture.
To make matters worse, many organizations are cloud-blind, with limited visibility into their cloud infrastructure. While defenders have become adept at logging and monitoring onsite operations, many are starting from scratch in the cloud. Meanwhile, providers themselves have inconsistent support for logging and monitoring. The result is that most organizations do not have the ability to detect even simple cloud attacks early on, which can lead to serious data breaches. Furthermore, while both customers and cloud providers must share responsibility for preventing data breaches, confusion over who is responsible for the different aspects of security is still common, making cloud hacking a top cybersecurity threat. Check out Chapter 13, "Cloud Breaches," in the Data Breaches book for an in-depth discussion and case studies on cloud data breaches.
2. A Dangerous New Twist on Ransomware
To pay or not to pay? That is the question—and it just got a lot harder to answer with the emergence of ransomware's latest trend: exposure threats.
In a classic ransomware case, criminals lock up an organization's data using strong encryption, and will only release the key if the victim pays up. If you have good backups, you may be able to recover your data without paying. Many organizations also choose not to pay for ethical reasons, refusing to fund criminal operations.
Criminals have seized upon a new tactic: threatening to release the victim's data to the world unless they receive their money ("exposure extortion"). This gives criminals a second opportunity to get their payout, leveraging the victim's fear of a data breach, and all the reputational damage/financial repercussions that go with it.
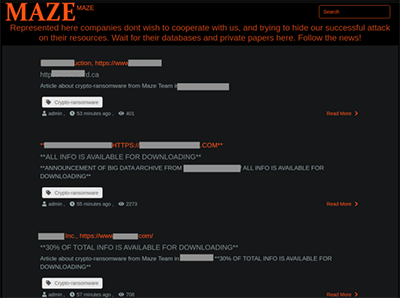
Screenshot of the Maze gang's web site. Image captured in LMG Security's malware lab. Copyright 2020, All rights reserved. Click to view full-sized image.
In December 2019, the Maze ransomware gang created a web site where they released data stolen from victims who did not "pay up." Among these victims was the City of Pensacola, which did not pay the $1 million ransom. In response, the Maze gang released 2 GB of the city's data (10%), stating "We've shown that our intentions are real."
The professional Sodinokibi ransomware gang similarly shifted tactics in December 2019. After hacking a large data center, CyrusOne, the criminals posted the following statement in a forum: "In case of refusal of payment—the data will either be sold to competitors or laid out in open sources. GDPR. Do not want to pay us—pay x10 times more to the government. No problems."
While the concept of exposure extortion is not new, combining it with ransomware is a brand-new twist with potentially far-reaching consequences. Ransomware has become a turnkey operation, with criminals peddling automated commercial toolkits that support scalable, large-scale deployment. The marriage of exposure threats with modern ransomware toolkits raises the specter that data exposure cases could become turnkey as well, leading to data breaches on a massive scale, making this one of the top cybersecurity threats for 2020. For more advice on responding to ransomware and extortion cases, read Chapter 11, "Extortion," in the Data Breaches book.
