- About This Book
- Trying to Define the Cloud
- Moving to AWS
- Essential Characteristics of AWS Cloud Computing
- Operational Benefits of AWS
- Cloud Provider Limitations
- Data Security at AWS
- Network Security at AWS
- Application Security at AWS
- Compliance in the AWS Cloud
- Migrating Applications
- The Well-Architected Framework
- The Well-Architected Tool
- In Conclusion
Application Security at AWS
Both Web and application servers hosted at AWS should always be located on private subnets. Private subnets are not directly accessible from the Internet. You may be wondering how to access what was supposed to be a public-facing application with no direct public access. The solution to this question is the absolute best practice to follow at AWS: for Web servers that customers across the Internet access, placing the load balancer on a public subnet, in front of the Web servers, provides the correct design solution. Customers requesting access to the application will be directed by DNS to the DNS name of the load balancer. The load balancer directs incoming traffic from the public subnet to the targeted Web servers hosted in the private subnets.
One load balancer type offered by AWS is the Application Load Balancer, which can perform authentication and SSL offload services. The end-to-end traffic pattern for a three-tier Web application can be designed using many encryption/decryption points, as shown in Figure 1-10 on its path from source to destination:
Web application firewall—A custom traffic filter in front of the Application Load Balancer protecting against malicious traffic.
Elastic Load Balancer (ELB)—Accepts only encrypted HTTPS traffic on port 443; provides secure sockets layer/transport layer security (SSL/TLS) decryption and, optionally, user authentication.
EC2 instance hosting Web application—EBS boot and data drives can be encrypted.
EC2 instance hosting application server—EBS boot and data drives can be encrypted.
Database server—EBS boot and data drives and data community can be encrypted, or Dynamo DB tables can be encrypted.
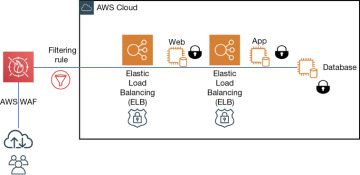
Figure 1-10 Encrypted traffic flow at AWS
