- Introduction
- What is the Internet?
- Streaming—A Disruptive Technology
- The Structure of the Internet
- Security: Connected, Ubiquitous Networks—Vulnerable to Malicious Hackers
- Privacy
- The Impact of E-Commerce
- Fostering Civic Participation and Engagement—Online Forums
- Network Neutrality
- The Digital Divide: Bandwidth, Skills, and Computers
- Intranets and Extranets
The Structure of the Internet
The Internet is made up of edge and backbone routers that direct traffic based on addresses contained within the headers of data packets. In an effort to reduce delays, Content Delivery Networks (CDNs) install servers at their own locations and that of the carrier’s site at the Internet’s edges, thus placing content closer to the end users that request it.
Edge Routers
Edge routers are located at the edge of a carrier’s network where they connect to customers and to other routers. They are often located at Points of Presence (POPs) where multiple providers connect to the Internet.
The edge of a network needs to support complex applications, protocols, and video. Edge routers must support multiple protocols, including Internet Protocol version 6 and version 4 (IPv6 and IPv4), Multi-Protocol Label Switching (MPLS), Wide Area Software Defined Networking (WA SDNs), and complex accounting software to track packet usage per customer. On MPLS networks, edge routers attach labels as described in Chapter 5, “Broadband Network Services,” that include information regarding addresses, protocol, and Quality of Service (QoS). For more information about IPv4 and IPv6 addressing protocols, see the section “Address Structures” later in this chapter.
In addition, edge routers commonly handle aggregated Digital Subscriber Line Access Multiplexer (DSLAM) traffic in various formats; therefore, routers need to support both newer and older variations of IP and Wide Area Software Defined Networking (WA SDN). See Chapter 5 for a discussion of WA SDN.
Edge routers also use addressing information to determine how to handle the data. See Figure 6-2 for an example of a router.

FIGURE 6-2 An edge router programmed with the features listed above. These features are not present in backbone routers. (Courtesy of Cisco Systems, Inc. Unauthorized use not permitted.)
Services on edge routers include the following (if a router is used in the core, it does not require the extensive services listed here):
Authentication that verifies the sender is indeed who he identifies himself to be when he logs on to networks.
Protected session setup that confirms that each multimedia session conforms to the features and QoS allowed to the computer making the request. This protects against fraud and ensures accurate billing.
Network Address Translation (NAT) addressing that translates external IP addresses to internal IP addresses, and vice versa.
Support for IPv4 and IPv6 addressing. IPv6 is designed to replace IPv4; it supports many more IP addresses than IPv4’s 4.3 billion addresses.
Layer 2 switching for creating Virtual Private Networks (VPNs) to communicate directly with databases and applications in data centers. (See Chapter 5 for a description of VPNs.)
Firewall software that protects networks from hackers.
Accounting to track subscriber packet usage in the event that carriers charge for usage.
QoS per application and per user for VoIP and video.
In addition to more intelligence, there are requirements for greater capacity in routers. This is caused by increasing use of video conferencing, greater demand for video streaming by residential customers, access to cloud-based services, and growth in mobile smartphone Internet browsing. Router ports now commonly support multiple 10Gbps as well as 100Gbps services. Total capacity of edge routers ranges from 1 to 3 terabits per second (Tbps). A terabit is the equivalent of 1,000 gigabits.
Aggregation Routers in Core Networks
Core routers carry the highest concentration of traffic. A single core router connects to multiple edge routers, aggregates traffic from these edge routers, and then sends it to distant cities and countries. If a single router doesn’t have the capacity to handle this aggregated traffic, multiple routers can be networked together. When this is done, the networked routers function as a single entity with a single management interface. This simplifies the carrier’s operations, upgrades, and remote diagnostics.
Networking routers together is commonly done through virtualization. (See the section “Virtual Network Function [VNF]—Transforming Hardware Nodes into Software Functions” in Chapter 4, “Managing Broadband Networks” for information on virtualization.) Virtualization enables multiple functions including routers to appear as individual pieces of hardware on servers that can be networked together. In addition, traffic is balanced among all the networked routers. If one router fails, the others absorb its traffic.
Ensuring Reliability in the Core and Edge
Routers sold to carriers and to large web sites such as Google and Amazon are designed for “five 9s” of reliability. This means that they offer 99.999 percent uptime. They are sold with hot-swappable cards that connect to other services and networks. If a card fails, it can be replaced without taking the router out of service. They are also offered with options for duplicate processor cards and often come standard with dual power supplies. Power supplies connect to sources of electricity. It’s also common for carriers to install duplicate routers that can be seamlessly brought online in the event of a failure. Duplicate routers are crucial at the edge, where if the router fails, all other networks and customers connected to it lose service.
Enhancing Internet Performance by Using Content Delivery Networks
Content Delivery Networks (CDNs) provide a number of services at the edge of the Internet that alleviate congestion on the Internet’s backbone. In its simplest form, a CDN reduces congestion by decreasing the distance that the traffic must travel. One way they accomplish this is by storing frequently requested web pages at their servers, nearer to the end users, often in a service provider’s location. This is referred to as caching. Many enterprises with large web sites use CDNs to replicate their web content at many edge locations to prevent delays at their web or e-commerce sites. For traffic that traverses the Internet backbone, CDNs use mathematical algorithms to map out the best paths for traffic to take.
Exchanging Data at Peering Points
Large multinational carriers are referred to as Tier 1 carriers. Tier 1 carriers own the majority of the high-speed lines that make up the Internet backbone. These carriers, all of whose networks are international, include Nippon Telegraph and Telephone Corporation (NTT) in Japan; Telefónica in Spain and Latin America; Deutsche Telekom in Germany; France Telecom in France; and AT&T, Sprint, and Verizon in the United States.
Regional carriers—which are referred to as Tier 2 carriers—also own core, backbone facilities. Comcast and Charter are considered Tier 2 carriers because their networks do not cover the entire country and they purchase backbone capacity from Tier 1 carriers. These Tier 1 and Tier 2 carriers interconnect with other carriers in places where they do not have coverage. These interconnections are referred to as peering points.
Network service providers transfer Internet Protocol (IP) traffic among one another at peering sites. Peering sites are also referred to as Internet exchanges and Network Access Points (NAPs). ISPs lease ports on the routers of other providers as a means of transferring IP traffic between networks. This enables carriers to send traffic that originated from their own customers to areas where they do not have network facilities, as demonstrated in Figure 6-3.
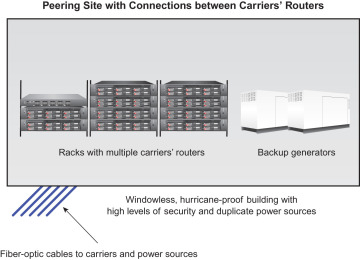
FIGURE 6-3 Traffic at peering points is routed between the facilities of multiple network operators.
Carriers that own peering points charge other carriers for connections to ports on their routers. However, traffic at these peering centers has the potential to create delays in the Internet if carriers lease too few ports from one another in an attempt to save money. If carriers exchange about the same amount of traffic, they often don’t charge one another under this arrangement. Security, routing, traffic policing, and Network Address Translation (NAT) take place at peering points.
Address Structures
Two universal addressing schemes, IPv4 and IPv6, are used to transmit messages from computers, smartphones, and tablet computers worldwide. The system of routing messages based on IP addresses is managed by 12 organizations that administer 13 clusters of servers, called root servers.
The Criticality of Root Servers
The root name server system was implemented in the 1990s. The Internet cannot function without root servers, which route messages to the correct organization. Root servers are critical for the sustainability, capacity, and survivability of the Internet. To lessen the system’s vulnerability to malicious actions such as Denial-of-Service (DoS) attacks, wherein millions of fake messages bombard a site, root servers balance incoming messages among multiple servers within each root. If one server within the root is brought down, other servers within the root handle the traffic. Ensuring protection against hackers is an ongoing endeavor.
The 13 Root Servers Worldwide
The Domain Name System (DNS) is the umbrella name of the Internet’s capability to translate alpha characters to numeric IP addresses within root servers. Carriers and organizations send traffic addressed to locations outside their networks to one of the 13 sets of root servers, usually the one nearest to them, to determine where to route these messages. The root servers, which are massive databases, translate alphabetic hostnames (gmail.com) into numeric IP addresses (193.22.1.126), and vice versa. Root servers are connected to peering exchanges where large carriers exchange traffic with each other. Each of the 12 organizations that operate the root servers has root servers located in multiple cities or countries. They each operate between 2 and 196 locations.
Examples of organizations that operate the 13 root servers are:
Each of the following organizations operates two sets of root servers:
Information Sciences Institute manages root servers U.S. Army Research Lab, which operates root servers in Los Angeles U.S.A. and in Miami U.S.A.
U.S. Army Research Lab manages root servers in Aberdeen Proving Ground, U.S. and San Diego, U.S.
WIDE operates 196 root servers, the most of any operator
Tracking and Managing Top-Level Domains
The Internet Corporation for Assigned Names and Numbers (ICANN) is the organization responsible for managing the technical aspects of the databases of domain names in root servers. It in effect manages the Internet’s address book. In a web or e-mail address such as name@companyname.com, the .com portion is the top-level domain name, and companyname is the domain name, which is also referred to as the secondary-level domain name. Every country has a top-level domain name. For example, for China, it’s .cn; for Russia, it’s .ru. In the United States, some top-level domain names include .edu and .mil for educational and military institutions, and.gov for the government.
Voting ICANN board members were appointed by the United States Department of Commerce until 2009 when the Department of Commerce had sole responsibility for these policies. However, increasing criticism by other countries regarding what they felt to be too much control by the United States of major aspects of the Internet has led to the establishment of international review and policy determination.
Two years after 2013 when Edward Snowden revealed multiple instances of United States government surveillance of other countries and their leaders, the international community began organizing increased efforts for representatives from additional countries to manage ICANN. After years of negotiations, technical leaders from multiple countries agreed on a framework where control of top level domains would be managed by an international group of technical people, governments, and representatives from private companies. A group made up of these representatives now controls ICANN.
The Inclusion of Non-Western Domain Names
Initially, addressing systems used only the Roman alphabet character set (A–Z, a–z, the digits 0–9, and the hyphen). However, pressure from countries that use other character systems eventually led to the inclusion of other alphabets for addresses. These non-Roman alphabets include Arabic, Persian, Chinese, Russian, Japanese, and Korean. China, South Korea, and Arabic-speaking nations had already started assigning non-Roman domain names. These addresses introduced the possibility of duplicate domain names because they were outside of the root system. This created pressure for ICANN to alter their addressing requirements and make the technical changes in the root system that translations from other alphabets require.
Transitioning to IPv6
The main addressing scheme used on the Internet was initially IPv4. IPv4 was developed in the 1970s and addresses are only 32 bits long. On January 31, 2011, the Internet Assigned Numbers Authority (IANA), which managed the central supply of Internet addresses at that time, gave out the last of their IPv4 addresses to each of the five regional Internet registries. By April 2011, the Asia Pacific region had given out all of their addresses, and the remaining four registries distributed all of their addresses within the next few years, Capacity is being depleted by the addition of new Internet-enabled wireless devices and the growing number of Internet users, particularly in Asia.
To ensure that they will be able to get new IP addresses, most organizations are now transitioning to the newer 128-bit IPv6 protocol, which is capable of accommodating billions of additional addresses. Most carriers have transitioned to IPv6. The IPv6 IEEE standard was published in 1998.
Most new routers, web browsers, and computers are compatible with both IPv4 and IPv6. The transition to IPv6 can be complex because it means assigning new addresses to every device with an IP address, including routers, firewalls, network management software, and all servers, including e-mail servers. In addition, it’s not a simple matter to determine which applications and devices are compatible with IPv6. Enterprises that transition to IPv6 often need to be able to handle messages that are still in the older IPv4 scheme. Encapsulating IPv6 addresses within IPv4 can address this problem. There are also software packages that support both protocols.

