Understanding Information Security Governance
Learn how to incorporate information security governance into your strategic cybersecurity plan.
Save 35% off the list price* of the related book or multi-format eBook (EPUB + MOBI + PDF) with discount code ARTICLE.
* See informit.com/terms
A prince or general can best demonstrate his genius by managing a campaign exactly to suit his objectives and his resources, doing neither too much nor too little. But the effects of genius show not so much in novel forms of action as in the ultimate success of the whole.
—On War, Carl Von Clausewitz
NIST SP 800-100, Information Security Handbook: A Guide for Managers, defines information security governance as follows:
Information security governance
The process of establishing and maintaining a framework and supporting management structure and processes to provide assurance that information security strategies are aligned with and support business objectives, are consistent with applicable laws and regulations through adherence to policies and internal controls, and provide assignment of responsibility, all in an effort to manage risk.
ITU-T X.1054, Governance of Information Security, defines information security governance as “the system by which an organization’s information security-related activities are directed and controlled.”
More generally, the term security governance encompasses governance concerns for cybersecurity, information security, and network security.
governance
Establishment of policies and continuous monitoring of their proper implementation by the members of the governing body of an organization. Governance includes the mechanisms required to balance the powers of the members (with the associated accountability) and their primary duty of enhancing the prosperity and viability of the organization.
2.1 Security Governance and Security Management
To better understand the role of security governance, it is useful to distinguish between information security governance (previously defined), information security management, and information security implementation/operations. ISO 27000 defines information security management as follows:
The supervision and making of decisions necessary to achieve business objectives through the protection of the organization’s information assets. Management of information security is expressed through the formulation and use of information security policies, procedures and guidelines, which are then applied throughout the organization by all individuals associated with the organization.
And information security implementation/operations can be defined in this fashion:
The implementation, deployment and ongoing operation of security controls defined within a cybersecurity framework.
Figure 2.1 suggests the hierarchical relationship between these three concepts. The security governance level communicates the mission priorities, available resources, and overall risk tolerance to the security management level. In essence, security governance is the process of developing a security program that adequately meets the strategic needs of the business. The security management level uses the information as inputs into the risk management process that realizes the security program. It then collaborates with the implementation/operations level to communicate security requirements and create a cybersecurity profile. The implementation/operations level integrates this profile into the system development life cycle and continuously monitors security performance. It executes or manages security-related processes related to current infrastructure on a day-to-day basis. The security management level uses monitoring information to assess the current profile and reports the outcomes of that assessment to the governance level to inform the organization’s overall risk management process.
security program
The management, operational, and technical aspects of protecting information and information systems. A security program encompasses policies, procedures, and management structure and mechanism for coordinating security activity.
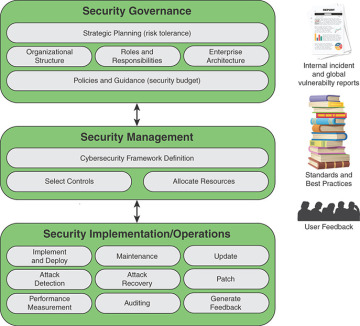
FIGURE 2.1 Information Security Management System Element
Figure 2.1 illustrates the key responsibilities at each level. As indicated, there is interaction among the three layers in the ongoing evolution of the information security management system (ISMS). In addition, three supplemental factors play roles. Internal security incident reports and global vulnerability reports from various sources help define the threat and level of risk that the organization faces in protecting its information assets. The numerous standards and best practices documents provide guidance on managing risk. User feedback comes from both internal users and external users who have access to the organization’s information assets. This feedback helps improve the effectiveness of policies, procedures, and technical mechanisms. Depending on the organization and its cybersecurity approach, each of the three factors plays a role to a greater or lesser extent at each level.
This chapter is devoted to security governance. Chapter 3, “Information Risk Assessment,” covers security management, and the succeeding chapters cover security implementation/operations.
