Data Center Integration
Deploying Azure Stack in your data center involves a number of tasks and processes. As with any enterprise system, Azure Stack requires a regular cadence of lifecycle management. The following looks at the different integration points you should consider while deploying and running Azure Stack in your data center.
Figure 3.26 is a high-level deployment diagram of an Azure Stack deployment with n number of scale units.
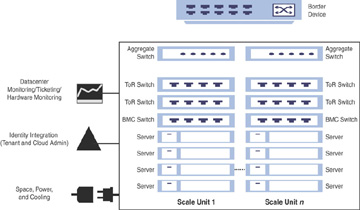
FIGURE 3.26 Deploying Azure Stack in your data center.
Deployment: Configuring Azure Stack in your data center involves certain manual and automated tasks. As Azure Stack is delivered as an integrated system you will not be setting up any hardware on your own; instead, you will purchase a deployment-ready rack-and-stack scale unit from one of the Microsoft OEM partners, ready to plug into your data center. You still must manually configure network switches and integrate with the border network on the network stack, in collaboration with your Azure Stack OEM partner. If you have a large deployment, you may need to consider these requirements for other scale units of your Azure Stack instance as well. When you power on your Azure Stack system, one of the very first configuration tasks would be to establish connectivity with AAD or ADFS, and so on.
Validation: Azure Stack is validated as an integrated system, where all components are tested together to perform a complete system validation. Configuration of hardware components such as NICs, HBAs, drives, network switches, servers, and so on will follow the traditional Windows Server tests with the Windows hardware kit lab (HLK). Furthermore, there will be additional tests and diagnostics run specific to Azure Stack integration on top of the HLK.
Patching and Update: Patching and updating involves applying pre-validated updates for software and firmware by Microsoft and hardware partners. This automated application of updates across the entire infrastructure is designed to not disrupt tenant workloads. Unlike Windows Server updates, Azure Stack updates are delivered as one package that contain updates for hardware, OS, and software. The updates will be delivered at a rapid cadence, letting you choose when to apply them within a given time frame depending on their business requirements. Should you not deploy an update before the given time frame, the scale unit will go out of support. This ensures that patching and updating in Azure Stack will always be reliable, single-sourced, and easy to use.
Monitoring and Service Management: The health state in Azure Stack is linked to alerts, and separates the health of cloud services from the cloud infrastructure. There are two types of health checks in Azure Stack:
Each component has its own notion of health and self-reports its own health status.
External system health tests that check how each component is used by the other components in Azure Stack.
Based on these two types, alerts will be generated based on the health status; these are actionable alerts that link to online troubleshooting guides for systematic guidance.
Figure 3.27 provides a high-level overview of how monitoring is enabled in Azure Stack.
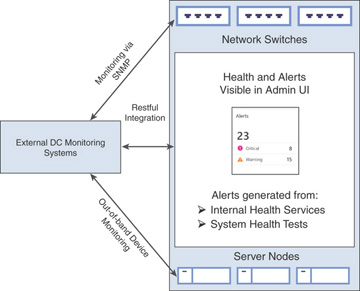
FIGURE 3.27 Monitoring Azure Stack.
As per your organizational requirements, you will also need to integrate Azure Stack with your existing monitoring systems. While Azure Stack does not allow you to install any monitoring agents, you can use existing connections from its own monitoring system such as Rest API, BMC, and SNMP to integrate with your existing monitoring solution and an information technology service management (ITSM) system.
