- 3.1 Introduction to Service-Orientation
- 3.2 Problems Solved by Service-Orientation
- 3.3 Effects of Service-Orientation on the Enterprise
- 3.4 Goals and Benefits of Service-Oriented Computing
- 3.5 Four Pillars of Service-Orientation
3.2 Problems Solved by Service-Orientation
To best appreciate why service-orientation emerged and how it is intended to improve the design of automation systems, we need to compare before and after perspectives. By studying some of the common issues that have historically plagued IT we can begin to understand the solutions proposed by this design paradigm.
Silo-based Application Architecture
In the world of business, delivering solutions capable of automating the execution of business tasks makes a great deal of sense. Over the course of IT’s history, the majority of such solutions have been created with a common approach of identifying the business tasks to be automated, defining their business requirements, and then building the corresponding solution logic (Figure 3.10).
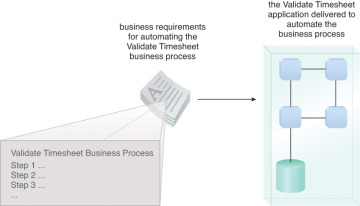
Figure 3.10 A ratio of one application for each new set of automation requirements has been common.
This has been an accepted and proven approach to achieving tangible business benefits through the use of technology and has been successful at providing a relatively predictable return on investment (Figure 3.11).
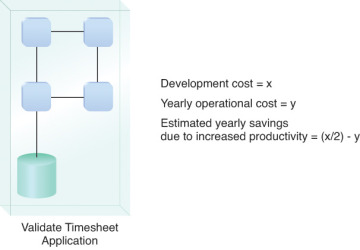
Figure 3.11 A sample formula for calculating ROI is based on a predetermined investment with a predictable return.
The ability to gain any further value from these applications is usually inhibited because their capabilities are tied to specific business requirements and processes (some of which will even have a limited lifespan). When new requirements and processes come our way we are forced to either make significant changes to what we already have or build a new application altogether.
In the latter case, although repeatedly building “disposable applications” is not the perfect approach, it has proven itself as a legitimate means of automating business. Let’s explore some of the lessons learned by first focusing on the positive.
Solutions can be built efficiently because they only need to be concerned with the fulfillment of a narrow set of requirements associated with a limited set of business processes.
The business analysis effort involved with defining the process to be automated is straightforward. Analysts are focused only on one process at a time and therefore only concern themselves with the business entities and domains associated with that one process.
Solution designs are tactically focused. Although complex and sophisticated automation solutions are sometimes required, the sole purpose of each is to automate just one or a specific set of business processes. This predefined functional scope simplifies the overall solution design as well as the underlying application architecture.
The project delivery lifecycle for each solution is streamlined and relatively predictable. Although IT projects are notorious for being complex endeavors, riddled with unforeseen challenges, when the delivery scope is well-defined (and doesn’t change), the process and execution of the delivery phases have a good chance of being carried out as expected.
Building new systems from the ground up allows organizations to take advantage of the latest technology advancements. The IT marketplace progresses every year to the extent that we fully expect technology we use to build solution logic today to be different and better tomorrow. As a result, organizations that repeatedly build disposable applications can leverage the latest technology innovations with each new project.
These and other common characteristics of traditional solution delivery provide a good indication as to why this approach has been so popular. Despite its acceptance, though, it has become evident that there is still much room for improvement.
It Can Be Highly Wasteful
The creation of new solution logic in a given enterprise commonly results in a significant amount of redundant functionality (Figure 3.12). The effort and expense required to construct this logic is therefore also redundant.
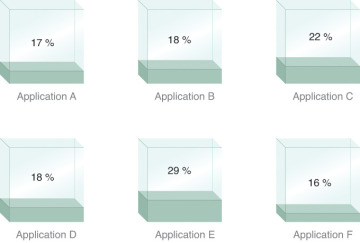
Figure 3.12 Different applications developed independently can result in significant amounts of redundant functionality. The applications displayed were delivered with various levels of solution logic that, in some form, already existed.
It’s Not as Efficient as It Appears
Because of the tactical focus on delivering solutions for specific process requirements, the scope of development projects is highly targeted. Therefore, there is the constant perception that business requirements will be fulfilled at the earliest possible time. However, by continually building and rebuilding logic that already exists elsewhere, the process is not as efficient as it could be if the creation of redundant logic could be avoided (Figure 3.13).
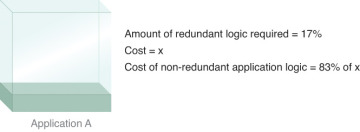
Figure 3.13 Application A was delivered for a specific set of business requirements. Because a subset of these business requirements had already been fulfilled elsewhere, Application A’s delivery scope is larger than it has to be.
It Bloats an Enterprise
Each new or extended application adds to the bulk of an IT environment’s system inventory (Figure 3.14). The ever-expanding hosting, maintenance, and administration demands can inflate an IT department in budget, resources, and size to the extent that IT becomes a significant drain on the overall organization.
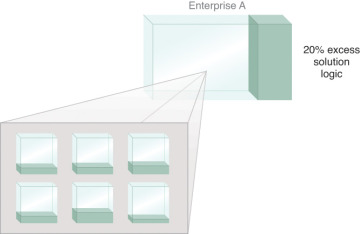
Figure 3.14 This simple diagram portrays an enterprise environment containing applications with redundant functionality. The net effect is a larger enterprise.
It Can Result in Complex Infrastructures and Convoluted Enterprise Architectures
Having to host numerous applications built from different generations of technologies and perhaps even different technology platforms often requires that each will impose unique architectural requirements. The disparity across these “siloed” applications can lead to a counter-federated environment (Figure 3.15), making it challenging to plan the evolution of an enterprise and scale its infrastructure in response to that evolution.
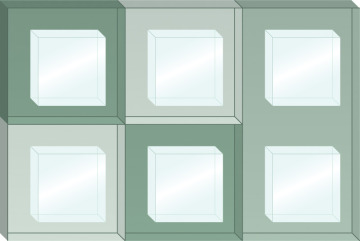
Figure 3.15 Different application environments within the same enterprise can introduce incompatible runtime platforms as indicated by the shaded zones.
Integration Becomes a Constant Challenge
Applications built only with the automation of specific business processes in mind are generally not designed to accommodate other interoperability requirements. Making these types of applications share data at some later point results in a jungle of convoluted integration architectures held together mostly through point-to-point patchwork (Figure 3.16) or requiring the introduction of large middleware layers.
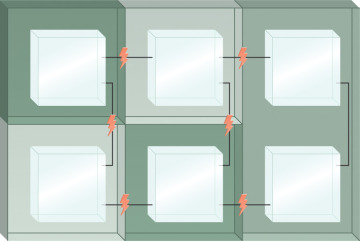
Figure 3.16 A vendor-diverse enterprise can introduce a variety of integration challenges, as expressed by the little lightning bolts that highlight points of concern when trying to bridge proprietary environments.
The Need for Service-Orientation
After repeated generations of traditional distributed solutions, the severity of the previously described problems has been amplified. This is why service-orientation was conceived. It very much represents an evolutionary state in the history of IT in that it combines successful design elements of past approaches with new design elements that leverage conceptual and technology innovation.
The consistent application of the eight design principles we listed earlier results in the widespread proliferation of the corresponding design characteristics:
increased consistency in how functionality and data is represented
reduced dependencies between units of solution logic
reduced awareness of underlying solution logic design and implementation details
increased opportunities to use a piece of solution logic for multiple purposes
increased opportunities to combine units of solution logic into different configurations
increased behavioral predictability
increased availability and scalability
increased awareness of available solution logic
When these characteristics exist as real parts of implemented services they establish a common synergy. As a result, the complexion of an enterprise changes as the following distinct qualities are consistently promoted.
Increased Amounts of Reusable Solution Logic
Within a service-oriented solution, units of logic (services) encapsulate functionality not specific to any one application or business process (Figure 3.17). These services are therefore classified as reusable (and agnostic) IT assets.
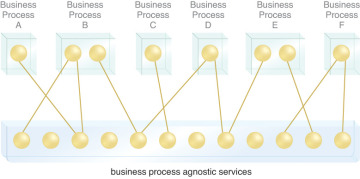
Figure 3.17 Business processes are automated by a series of business process–specific services (top layer) that share a pool of business process–agnostic services (bottom layer). These layers correspond to service models described in Chapter 5.
Reduced Amounts of Application-Specific Logic
Increasing the amount of solution logic not specific to any one application or business process decreases the amount of required application-specific (or “non-agnostic”) logic (Figure 3.18). This blurs the lines between standalone application environments by reducing the overall quantity of standalone applications. (See the Service-Orientation and the Concept of “Application” section later in this chapter.)
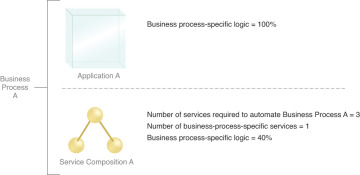
Figure 3.18 Business Process A can be automated by either Application A or Service Composition A. The delivery of Application A can result in a body of solution logic that is all specific to and tailored for the business process. Service Composition A would be designed to automate the process with a combination of reusable services and 40% of additional logic specific to the business process.
Reduced Volume of Logic Overall
The overall quantity of solution logic is reduced because the same solution logic is shared and reused to automate multiple business processes, as shown in Figure 3.19.

Figure 3.19 The quantity of solution logic shrinks as an enterprise transitions toward a standardized service inventory comprised of “normalized” services. (Service normalization is explained further at the end of Chapter 5.)
Inherent Interoperability
Common design characteristics consistently implemented result in solution logic that is naturally aligned. When this carries over to the standardization of service contracts and their underlying data models, a base level of automatic interoperability is achieved across services, as illustrated in Figure 3.20. (See the Service-Orientation and the Concept of “Integration” section later in this chapter.)
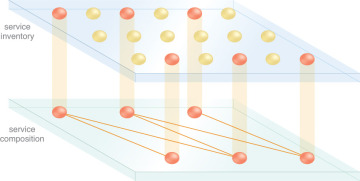
Figure 3.20 Services from different parts of a service inventory can be combined into new compositions. If these services are designed to be intrinsically interoperable, the effort to assemble them into new composition configurations is significantly reduced.

